Cybersecurity incidents are no longer a matter of “if” but “when.” While organizations invest heavily in preventive security measures, few adequately plan for the inevitable financial impact of security breaches. The average cost of a data breach now exceeds $4.45 million globally, yet most organizations lack accurate estimates of their potential incident response costs, leading to budget shortfalls, inadequate preparation, and suboptimal response decisions during critical moments.
Incident Response Cost Calculator | Security Budget PlanningEstimate the financial impact of security incidents. Compare in-house vs. outsourced costs and identify highest-ROI security investments for your organization.![]() Compare Security Investment ROI
Compare Security Investment ROI The financial implications of cybersecurity incidents extend far beyond immediate technical remediation. Organizations face a complex web of costs including regulatory fines, legal fees, customer notification expenses, business disruption, reputation damage, and long-term competitive impacts. Understanding and planning for these costs isn’t just about financial preparedness—it’s about making strategic decisions that can significantly reduce overall incident impact and organizational risk.
The financial implications of cybersecurity incidents extend far beyond immediate technical remediation. Organizations face a complex web of costs including regulatory fines, legal fees, customer notification expenses, business disruption, reputation damage, and long-term competitive impacts. Understanding and planning for these costs isn’t just about financial preparedness—it’s about making strategic decisions that can significantly reduce overall incident impact and organizational risk.
The Hidden Economics of Cybersecurity Incidents
Beyond the Headlines: Understanding Total Cost Impact
When cybersecurity incidents make headlines, the focus often centers on the number of records compromised or the immediate technical details of the attack. However, the true financial impact encompasses multiple cost categories that many organizations fail to anticipate:
 Direct Response Costs
Direct Response Costs
- Forensic Investigation: Digital forensics experts, legal discovery, and evidence preservation
- Incident Response Team: Internal staff time and external consultant fees
- System Recovery: Infrastructure rebuilding, data restoration, and security enhancements
- Communication Management: Public relations, crisis communications, and stakeholder updates
Data Privacy Compliance Fine CalculatorCalculate potential fines and penalties for data privacy violations across GDPR, CCPA, HIPAA, and other privacy laws.Privacy Compliance Calculator
 Regulatory and Legal Costs
Regulatory and Legal Costs
- Compliance Fines: Penalties under GDPR, CCPA, HIPAA, and other privacy regulations
- Legal Fees: Defense against lawsuits, regulatory proceedings, and contract disputes
- Audit Requirements: Mandatory security assessments and compliance demonstrations
- Ongoing Monitoring: Enhanced oversight and reporting requirements
Business Disruption Costs
- Operational Downtime: Lost productivity during system outages and recovery
- Revenue Impact: Cancelled contracts, delayed projects, and lost business opportunities
- Customer Churn: Long-term customer loss due to trust erosion
- Market Value: Stock price impacts and valuation reductions
Long-Term Strategic Costs
- Insurance Premium Increases: Higher cybersecurity insurance costs following incidents
- Enhanced Security Investments: Mandatory improvements to prevent future incidents
- Competitive Disadvantage: Market position loss due to reputation damage
- Talent Acquisition: Increased costs to attract cybersecurity professionals
The Regulatory Compliance Multiplier Effect
Modern privacy regulations have fundamentally changed the cost structure of cybersecurity incidents. What once might have been managed as internal technical issues now trigger complex regulatory obligations with significant financial implications.
GDPR Impact Analysis Under the General Data Protection Regulation, organizations face fines up to €20 million or 4% of annual global turnover—whichever is higher. Beyond monetary penalties, GDPR requires:
- 72-Hour Notification: Immediate regulatory reporting with specific technical details
- Individual Notifications: Direct communication to affected data subjects within defined timeframes
- Documentation Requirements: Comprehensive incident documentation and response evidence
- Remediation Mandates: Specific technical and organizational measures to prevent recurrence
CCPA/CPRA Considerations California’s privacy laws introduce additional complexity with:
- Consumer Rights: Extensive individual notification and response requirements
- Statutory Damages: Per-consumer penalties that can quickly escalate with large-scale incidents
- Attorney General Authority: State-level enforcement with broad investigative powers
- Private Right of Action: Individual lawsuits for specific categories of data breaches
Industry-Specific Regulations
- HIPAA (Healthcare): Patient notification requirements and HHS oversight with potential criminal liability
- PCI DSS (Payment Cards): Card brand fines, forensic investigation mandates, and ongoing compliance monitoring
- SOX (Public Companies): Material disclosure requirements and internal control assessments
- FERPA (Education): Student record protection with federal funding implications
Strategic Cost Planning: The In-House vs. Outsourced Decision
Evaluating Internal Response Capabilities
Organizations face a critical strategic decision when planning incident response capabilities: building internal teams versus relying on external specialists. This decision has profound cost implications that extend beyond immediate incident response expenses.
Internal Team Advantages
- Immediate Availability: No waiting for external teams to mobilize during critical first hours
- Organizational Knowledge: Deep understanding of systems, processes, and business context
- Cost Predictability: Fixed salary costs rather than variable consulting fees
- Ongoing Value: Internal teams provide continuous security value beyond incident response
Internal Team Challenges
- Skill Gaps: Difficulty maintaining expertise across all incident response disciplines
- Capacity Constraints: Limited ability to scale during major incidents or multiple simultaneous events
- Technology Costs: Significant investment in specialized forensic and analysis tools
- Training Requirements: Ongoing education to maintain cutting-edge incident response capabilities
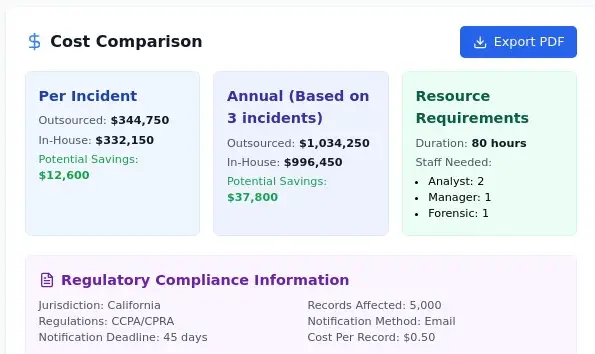
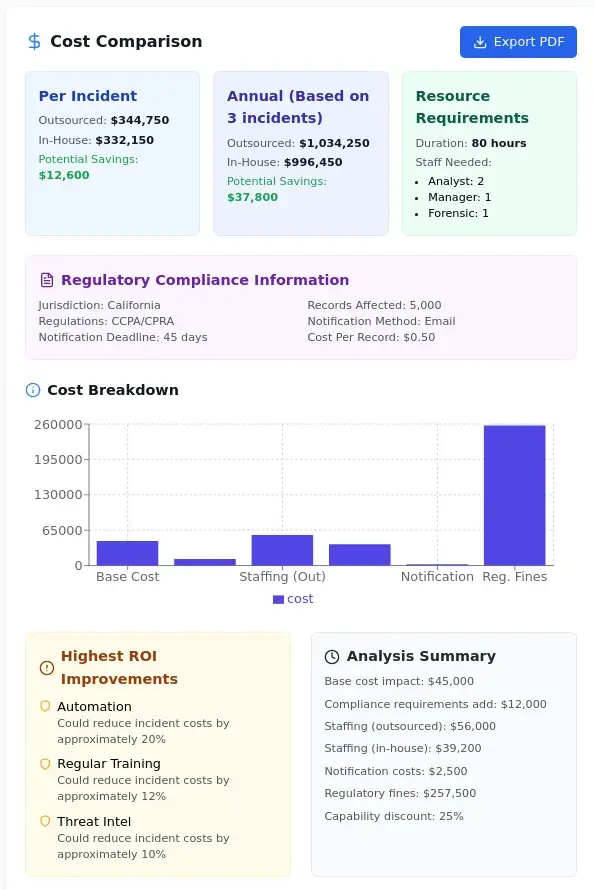
Cost Analysis: Internal vs. External Response
Based on comprehensive industry analysis, typical incident response costs vary significantly between internal and external approaches:
Per-Incident Cost Comparison (Medium Severity Data Breach)
- Outsourced Response: $344,750 average total cost
- In-House Response: $332,150 average total cost
- Potential Annual Savings: $37,800 (assuming 3 incidents annually)
However, these numbers require careful interpretation. While in-house response may show lower per-incident costs, organizations must consider:
Hidden Internal Costs
- Opportunity Cost: Internal team time diverted from proactive security initiatives
- Skill Development: Training and certification costs to maintain response capabilities
- Tool Licensing: Expensive forensic software and analysis platforms
- Staff Retention: Premium compensation required to retain incident response expertise
External Response Value Proposition
- Specialized Expertise: Access to specialists in specific incident types and attack vectors
- Surge Capacity: Ability to scale response teams for major incidents
- Latest Tools: Access to cutting-edge forensic and analysis technologies
- Legal Protection: Potential attorney-client privilege protection for investigation findings
Hybrid Response Models: Optimizing Cost and Capability
Many organizations adopt hybrid approaches that balance cost efficiency with response effectiveness:
Core Internal Capabilities
- Initial Response Coordination: Internal team manages immediate containment and communication
- Business Continuity: Internal staff ensures operational systems remain functional
- Stakeholder Management: Internal teams manage executive, legal, and regulatory communications
- Vendor Coordination: Internal resources manage external specialist integration
External Specialist Integration
- Advanced Forensics: External experts for complex malware analysis and attribution
- Specialized Compliance: External counsel for regulatory response and legal strategy
- Technical Recovery: External specialists for complex system rebuilding and security enhancement
- Independent Validation: Third-party assessment of response effectiveness and completeness
The ROI of Incident Response Investment
Quantifying Prevention vs. Response Investment
Organizations often struggle to balance investments in preventive security measures versus incident response capabilities. Understanding the ROI of different approaches enables more strategic resource allocation.
Automation Impact on Response Costs Investment in incident response automation can reduce costs by approximately 20% through:
- Faster Detection: Automated monitoring reduces time to discovery, limiting incident scope
- Streamlined Response: Orchestrated response workflows reduce manual coordination overhead
- Consistent Documentation: Automated logging ensures comprehensive incident documentation
- Reduced Escalation: Automated containment prevents incidents from becoming major breaches
Regular Training ROI Comprehensive incident response training programs can reduce incident costs by approximately 12% through:
- Improved Initial Response: Better trained staff make fewer critical errors during initial response
- Faster Coordination: Teams that train together respond more efficiently under pressure
- Reduced Panic: Training reduces stress-induced poor decision making during actual incidents
- Better Communication: Trained teams communicate more effectively with stakeholders and external parties
Threat Intelligence Integration Strategic threat intelligence programs can reduce incident costs by approximately 10% through:
- Earlier Warning: Advanced notice of targeting enables proactive defensive measures
- Context-Aware Response: Understanding attacker methods improves response efficiency
- Attribution Assistance: Better understanding of adversary capabilities focuses investigation efforts
- Preventive Insights: Intelligence about attack methods prevents similar future incidents
Data Breach Cost Calculator Integration
Understanding incident response costs requires comprehensive analysis of broader data breach financial impacts. Organizations can leverage specialized tools like the Data Breach Cost Calculator to understand how incident response investments fit within overall breach cost management strategies.
Comprehensive Cost Modeling The data breach cost calculator provides deeper analysis of:
- Industry-Specific Cost Factors: Healthcare, financial services, and technology sectors face different cost profiles
- Geographic Variations: Regional differences in regulatory fines and legal costs
- Breach Size Scaling: How costs change with the number of records compromised
- Time-to-Containment Impact: The relationship between response speed and total costs
Strategic Investment Decisions Combined analysis enables organizations to:
- Optimize Resource Allocation: Balance preventive security investments with response capability development
- Justify Budget Requests: Provide data-driven business cases for security investments
- Benchmark Performance: Compare organizational costs against industry averages
- Identify Improvement Opportunities: Pinpoint specific areas where investments yield highest returns
Regulatory Fine Analysis and Mitigation
Understanding Fine Calculation Methodologies
Regulatory fines for cybersecurity incidents vary significantly based on multiple factors that organizations must understand to accurately estimate potential costs.
GDPR Fine Calculation Factors European regulators consider numerous elements when determining penalties:
- Nature and Severity: Type of data compromised and scope of individual impact
- Intentionality: Whether the breach resulted from deliberate actions or negligence
- Cooperation Level: Organization’s collaboration with regulatory investigation
- Previous Violations: History of compliance issues and prior enforcement actions
- Remediation Efforts: Speed and effectiveness of incident response and notification
CCPA/CPRA Penalty Structure California’s privacy laws establish specific penalty frameworks:
- Statutory Damages: $100-$750 per consumer for specific violation categories
- Civil Penalties: Up to $2,500 per violation for general violations, $7,500 for intentional violations
- Attorney General Discretion: Broad authority to negotiate settlement terms
- Private Right of Action: Individual lawsuits for specific categories of personal information
Industry-Specific Considerations Different sectors face unique regulatory cost profiles:
- Healthcare (HIPAA): OCR fines ranging from $137-$1.9 million based on violation scope
- Financial Services: Multiple regulators (OCC, FDIC, Fed) with overlapping jurisdiction
- Education (FERPA): Federal funding suspension as primary enforcement mechanism
- Payment Cards (PCI DSS): Card brand fines and forensic investigation requirements
Fine Mitigation Strategies
Understanding potential regulatory costs enables organizations to develop strategies that minimize financial exposure while ensuring compliance.
Proactive Compliance Investment Organizations can leverage tools like Fine My Data to understand their specific regulatory risk profile and develop targeted compliance strategies:
- Jurisdiction Mapping: Understanding which regulations apply to specific data types and geographic regions
- Penalty Calculation: Accurate estimates of potential fines based on organizational data holdings
- Compliance Gap Analysis: Identification of specific areas where additional investment reduces fine risk
- Cost-Benefit Analysis: Balancing compliance investment against potential fine exposure
Response Strategy Optimization Effective incident response can significantly reduce regulatory penalties:
- Rapid Notification: Meeting or exceeding regulatory timeline requirements demonstrates good faith compliance
- Comprehensive Documentation: Detailed incident records show organizational commitment to transparency
- Remediation Evidence: Clear demonstration of steps taken to prevent future incidents
- Cooperation: Proactive engagement with regulators rather than defensive positioning
Incident Response Maturity and Cost Optimization
Assessing Current Capabilities
Organizations must understand their current incident response maturity to make informed investment decisions and accurately estimate potential costs.
Capability Assessment Framework Comprehensive incident response evaluation should examine:
- Detection Capabilities: Time to discovery for different incident types
- Response Coordination: Effectiveness of internal and external team coordination
- Communication Management: Quality of stakeholder and public communications
- Technical Recovery: Speed and completeness of system restoration
- Lessons Integration: Ability to improve security based on incident experience
Maturity Level Cost Implications Organizations at different maturity levels face significantly different incident costs:
- Ad Hoc Response: Highest costs due to inefficient coordination and poor decision making
- Developing Capabilities: Moderate costs with inconsistent performance across incident types
- Managed Response: Lower costs through established processes and trained teams
- Optimized Response: Lowest costs through continuous improvement and advanced automation
Assessment Tools and Benchmarking Organizations can evaluate their incident response maturity using specialized assessment tools like the IR Maturity Assessment to:
- Identify Capability Gaps: Specific areas where investment will reduce incident costs
- Benchmark Performance: Compare organizational capabilities against industry standards
- Prioritize Improvements: Focus investment on areas with highest cost reduction potential
- Track Progress: Measure improvement over time and validate investment effectiveness
Building Cost-Effective Response Capabilities
Graduated Investment Strategy Organizations should build incident response capabilities systematically to optimize cost-effectiveness:
Phase 1: Foundation Building (Months 1-6)
- Basic Response Plans: Documented procedures for common incident types
- Communication Frameworks: Clear escalation and notification processes
- Essential Tools: Basic forensic capabilities and communication platforms
- Initial Training: Core team training on fundamental response procedures
Phase 2: Capability Enhancement (Months 6-18)
- Advanced Detection: Enhanced monitoring and alerting capabilities
- Specialized Expertise: Training or hiring for specific incident response disciplines
- Process Automation: Workflow tools to streamline response coordination
- External Relationships: Contracts with external specialists and legal counsel
Phase 3: Optimization and Integration (Months 18+)
- Continuous Improvement: Regular assessment and enhancement of response capabilities
- Advanced Analytics: Metrics and dashboards to optimize response performance
- Cross-Functional Integration: Alignment with business continuity and risk management
- Proactive Capabilities: Threat hunting and intelligence integration
Industry-Specific Cost Considerations
Healthcare: HIPAA and Patient Trust
Healthcare organizations face unique incident response cost challenges due to strict regulatory requirements and the sensitive nature of patient data.
Regulatory Cost Factors
- OCR Investigations: Department of Health and Human Services oversight with potential criminal referrals
- State Notification Requirements: Individual state breach notification laws with varying timelines
- Patient Notification: Direct communication to affected individuals with specific content requirements
- Business Associate Liability: Potential costs from third-party breaches affecting healthcare data
Operational Impact Considerations
- Patient Care Disruption: Costs associated with delayed or cancelled medical procedures
- EHR System Recovery: Extensive costs for electronic health record system restoration
- Medical Device Security: Specialized expertise required for connected medical device incidents
- Provider Network Impact: Costs from disruption to affiliated healthcare providers
Strategic Cost Mitigation Healthcare organizations can reduce incident costs through:
- Proactive Risk Assessment: Regular evaluation of connected medical devices and third-party systems
- Enhanced Staff Training: Specialized training on healthcare privacy requirements
- Business Associate Management: Robust contracts and oversight of third-party healthcare vendors
- Incident Response Specialization: Investment in healthcare-specific incident response expertise
Financial Services: Regulatory Complexity and Customer Trust
Financial institutions face complex regulatory environments and high customer trust expectations that significantly impact incident response costs.
Multi-Regulator Environment
- Federal Banking Regulators: OCC, FDIC, and Federal Reserve with overlapping jurisdiction
- Securities Regulators: SEC and FINRA requirements for investment advisors and broker-dealers
- State Regulators: Individual state banking and insurance commission requirements
- Payment Card Industry: PCI DSS compliance with card brand enforcement
Customer Impact Amplification
- Account Monitoring: Enhanced monitoring services for affected customers
- Fraud Reimbursement: Direct financial liability for unauthorized account activity
- Credit Monitoring: Extended credit monitoring services for identity theft protection
- Customer Communication: Extensive communication requirements to maintain trust
Specialized Response Considerations
- Market Impact: Potential stock price and market confidence implications
- Trading Disruption: Costs associated with trading platform outages or compromises
- Regulatory Reporting: Complex and time-sensitive regulatory notification requirements
- Forensic Banking Expertise: Specialized knowledge of financial systems and attack vectors
Technology Companies: Intellectual Property and Competitive Advantage
Technology organizations face unique risks related to intellectual property theft and competitive intelligence gathering.
IP Protection Costs
- Source Code Analysis: Comprehensive review of potentially compromised development systems
- Patent and Trade Secret Impact: Assessment of intellectual property exposure and competitive harm
- Customer Data Protection: Costs associated with protecting customer and partner data
- Development Process Security: Enhanced security for software development and deployment pipelines
Customer and Partner Impact
- SaaS Service Disruption: Costs from interrupted service delivery to customers
- Partner Notification: Communication to technology partners and integration providers
- Certification Impact: Potential loss of security certifications and compliance status
- Market Confidence: Impact on customer acquisition and partner relationships
Emerging Cost Factors and Future Considerations
Artificial Intelligence and Automated Attacks
The emergence of AI-powered cyberattacks is changing the incident response cost landscape:
Enhanced Attack Sophistication
- Longer Discovery Times: AI-powered attacks that evade traditional detection methods
- Increased Investigation Complexity: Advanced forensic analysis required for AI-assisted attacks
- Broader Impact Scope: Automated attacks that can simultaneously target multiple systems
- Attribution Challenges: Difficulty determining human vs. automated attack components
Response Capability Requirements
- AI-Skilled Personnel: Incident response teams with artificial intelligence expertise
- Advanced Analytics: Machine learning tools for attack pattern recognition
- Automated Response: AI-powered response capabilities to match attack speed
- Continuous Adaptation: Response capabilities that evolve with AI attack sophistication
Quantum Computing Implications
The eventual emergence of quantum computing will fundamentally change cybersecurity incident costs:
Cryptographic Transition Costs
- Legacy System Updates: Massive costs to update encryption across organizational systems
- Compliance Timeline Pressure: Regulatory deadlines for quantum-safe cryptography adoption
- Retroactive Decryption Risk: Potential exposure of previously encrypted data
- Supply Chain Coordination: Costs to ensure vendor quantum-readiness
Strategic Planning Requirements
- Timeline Assessment: Understanding when quantum threats become practical concerns
- Investment Prioritization: Balancing current security needs with quantum preparation
- Capability Development: Building organizational expertise in post-quantum cryptography
- Risk Communication: Explaining quantum risks to executives and stakeholders
Supply Chain Attack Evolution
Increasingly sophisticated supply chain attacks are changing incident response cost calculations:
Extended Investigation Scope
- Vendor Assessment: Comprehensive evaluation of third-party security practices
- Multi-Organization Coordination: Complex coordination with affected vendors and customers
- Attribution Complexity: Difficulty determining whether vendors or customers are primary targets
- Remediation Coordination: Synchronized response across multiple organizations
Long-Term Impact Costs
- Vendor Relationship Changes: Costs associated with changing suppliers and service providers
- Enhanced Due Diligence: Increased costs for vendor security assessment and ongoing monitoring
- Insurance Implications: Changes in cyber insurance coverage and pricing
- Regulatory Evolution: New compliance requirements for supply chain security
Strategic Implementation: Building Your Cost Estimation Framework
Organizational Assessment and Baseline Development
Effective incident response cost planning begins with comprehensive organizational assessment:
Current State Analysis
- Historical Incident Review: Analysis of past incidents and associated costs
- Capability Inventory: Assessment of current incident response capabilities and resources
- Regulatory Environment: Understanding of applicable regulations and compliance requirements
- Business Context: Evaluation of organizational risk profile and business model implications
Cost Baseline Establishment
- Industry Benchmarking: Comparison with similar organizations and industry averages
- Scenario Modeling: Development of cost estimates for various incident types and severities
- Resource Requirements: Assessment of personnel, technology, and external service needs
- Budget Allocation: Strategic distribution of incident response budget across capabilities
Continuous Improvement and Cost Optimization
Regular Assessment and Updates
- Quarterly Cost Reviews: Regular evaluation of actual incident costs versus estimates
- Threat Landscape Updates: Adjustment of cost models based on evolving attack methods
- Regulatory Changes: Updates to cost estimates based on new compliance requirements
- Technology Evolution: Adjustment for new security technologies and response capabilities
Strategic Investment Planning
- ROI Analysis: Evaluation of investment options based on cost reduction potential
- Capability Gaps: Identification of areas where additional investment provides highest value
- External Partnership Evaluation: Regular assessment of outsourcing versus internal capability development
- Insurance Optimization: Strategic use of cyber insurance to manage incident cost risk
Conclusion: Strategic Financial Preparedness for Cyber Incidents
Cybersecurity incidents are inevitable, but their financial impact doesn’t have to be catastrophic. Organizations that understand the true cost of incidents and invest strategically in response capabilities will be better positioned to minimize financial damage while maintaining business continuity and stakeholder trust.
IR Maturity Assessment | Free Incident Response Evaluation ToolEvaluate your organization’s incident response capabilities in minutes. Get personalized insights and actionable recommendations.Free Incident Response Evaluation ToolIR Maturity Assessment Team

The future belongs to organizations that recognize incident response as a strategic business capability worthy of significant investment and careful planning. By understanding costs, optimizing capabilities, and preparing for emerging threats, organizations can transform cybersecurity incidents from existential threats into manageable business challenges.
Ready to understand your organization’s incident response cost exposure? Use our comprehensive incident response cost estimator to model potential scenarios and identify opportunities for strategic investment and cost optimization. Your preparation today determines your resilience tomorrow.
For comprehensive cybersecurity cost analysis, explore our complete suite of assessment tools: Data Breach Cost Calculator for overall breach impact modeling, Fine My Data for regulatory penalty assessment, and IR Maturity Assessment for incident response capability evaluation.