The ransomware landscape has undergone a dramatic transformation throughout 2025, with law enforcement disruptions creating both chaos and opportunity within the cybercriminal ecosystem. While Operation Cronos dismantled LockBit’s infrastructure in early 2024, the void left by the once-dominant group has spawned a more fragmented, competitive, and paradoxically more dangerous threat environment. As we approach the end of 2025, ransomware attacks have reached unprecedented levels, with sophisticated Ransomware-as-a-Service (RaaS) platforms democratizing cybercrime and enabling affiliates worldwide to launch devastating attacks with minimal technical expertise.
The Evolution of Ransomware-as-a-Service
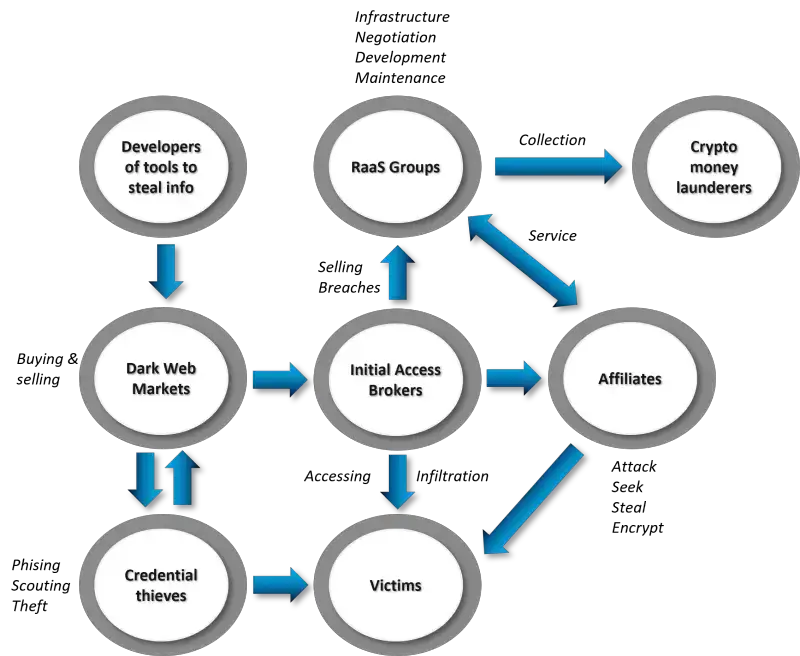
Ransomware-as-a-Service has fundamentally transformed cybercrime from an activity requiring elite technical skills into an accessible, plug-and-play business model. RaaS operators function like legitimate software vendors, developing and maintaining ransomware infrastructure while recruiting affiliates to execute attacks. The model typically operates on a profit-sharing basis, with developers taking anywhere from 20% to 40% of ransom payments while affiliates keep the remainder.
Spanish Cyberterrorism: 19-Year-Old Student Arrested for Massive Political Data Leak Targeting Prime Minister Pedro SánchezHow a computer science student from Gran Canaria orchestrated one of Spain’s most significant political data breaches from his parents’ home, exposing thousands of high-profile figures in what authorities are calling an act of cyberterrorism Breaking News: Unprecedented Political Data Leak Rocks Spain In a dramatic turn of events that![]() Breached CompanyBreached Company
Breached CompanyBreached Company
What makes the current threat landscape particularly concerning is that the top ten ransomware groups now account for just 56% of all victims, down from 71% in Q1 2025. This fragmentation indicates that successful takedowns of major operators no longer significantly impact overall attack volumes—affiliates simply migrate to new platforms or establish independent operations.
LockBit’s Fall from Grace
For years, LockBit stood as the most prolific RaaS operation, claiming over 3,500 victims since its 2019 debut. The group’s infrastructure, affiliate network, and brand recognition made it the gold standard for ransomware operations. However, Operation Cronos in February 2024 marked the beginning of LockBit’s decline.
The coordinated law enforcement action, led by international agencies including the FBI, UK’s National Crime Agency, and Europol, resulted in the seizure of LockBit’s infrastructure and the subsequent sanctioning of its founder, Russian national Dmitry Yuryevich Khoroshev. Law enforcement gained control of LockBit’s data leak sites, using them to reveal information about the group’s operations, and discovered that despite promises to the contrary, LockBit did not delete victims’ data after receiving ransom payments.
While LockBit attempted to rebuild and continue operations, the damage proved insurmountable. By late 2025, the group no longer ranks among the top fifteen most active ransomware operations, a stunning fall for what was once the industry’s undisputed leader.
The disruption of LockBit sent shockwaves through the ransomware ecosystem, displacing thousands of affiliates who had relied on the platform’s robust infrastructure and professional operations. These displaced actors quickly sought new homes, accelerating the rise of competing RaaS platforms that were eager to capture market share.
Qilin: The Reigning Champion of 2025
Qilin (also known as Agenda) has emerged as the most active and dangerous ransomware operation in 2025, filling the vacuum left by LockBit’s collapse. The group has demonstrated remarkable growth, averaging 75 victims per month in Q3 2025—double its activity from earlier in the year. In both June and July 2025, Qilin led the ransomware landscape with 86 and 73 victims respectively, accounting for approximately 17% of all reported attacks during those months.
Technical Sophistication
Qilin’s success stems from its sophisticated technical implementation and business model. The group’s ransomware, written in Rust, provides exceptional cross-platform capabilities targeting Windows, Linux, and ESXi environments. Rust’s memory-safe properties and efficient performance make the malware particularly difficult to detect and reverse-engineer, while its cross-platform nature allows affiliates to target diverse infrastructure.
The group employs a sophisticated double-extortion model, encrypting victim data while simultaneously exfiltrating sensitive information. Qilin’s dedicated leak site, hosted on Tor, features customized company identifiers and account details for victims who refuse to pay. Throughout 2025, the group has continuously enhanced its platform, adding spam campaign capabilities, DDoS attack functions, automated network propagation, automated ransom negotiation panels, and even “in-house journalists” to assist affiliates with crafting pressure campaigns.
Strategic Targeting and Financial Impact
Since its 2022 emergence, Qilin has been linked to 926 attacks across 226 countries, with 168 confirmed incidents resulting in the breach of over 2.3 million records and the theft of 116 terabytes of data. The group’s confirmed attacks alone have exfiltrated 47 terabytes of information, demonstrating the massive scale of their data theft operations.
Qilin’s targeting reflects a calculated approach focused on high-value sectors. Manufacturing accounts for approximately 23% of the group’s victims, followed by professional and scientific services at 18% and wholesale trade at 10%. The financial sector has proven particularly lucrative, with Qilin conducting a sustained campaign against South Korean financial institutions in August and September 2025, compromising 30 organizations in just two months.
One of Qilin’s most significant attacks targeted Synnovis Laboratories, an NHS partner in the United Kingdom, resulting in the disruption of services at multiple hospitals and forcing the cancellation of over 10,000 appointments and procedures. More recently, on November 5, 2025, Qilin claimed responsibility for breaching Habib Bank AG Zurich, allegedly stealing 2.5 terabytes of sensitive customer and corporate data, including financial records, system source code, and personal identification documents.
Affiliate Program Excellence
Qilin’s rapid ascension can be largely attributed to its attractive affiliate program. The group offers up to 85% revenue share to affiliates—one of the most generous splits in the RaaS ecosystem. This aggressive commission structure became particularly effective following RansomHub’s sudden disappearance in April 2025, when displaced affiliates flocked to Qilin’s platform. The influx of experienced operators contributed to a 280% jump in attack claims between late April and October 2025.
In-Depth Technical Document on the CrowdStrike BSOD Incident@cisomarketplace CrowdStrike vs Microsoft: Impact and Fallout Explained Get a comprehensive understanding of the ongoing issue between CrowdStrike and Microsoft. Explore the potential impact on businesses worldwide and uncover the vulnerabilities it exposes. Find out how this incident affects Microsoft computers and learn why it’s crucial to have foolproof cybersecurity.![]() Breached CompanyBreached Company
Breached CompanyBreached Company
Akira: Speed and Aggression
Akira ransomware has established itself as one of the fastest-moving and most aggressive threat groups in the current landscape. Since emerging in March 2023, Akira has impacted over 250 organizations globally and claimed approximately $244.17 million in ransomware proceeds as of late September 2025. The group’s rapid evolution and sophisticated tactics have made it a primary concern for critical infrastructure defenders.
Lightning-Fast Attack Chains
What distinguishes Akira from competitors is the remarkable speed of its attack chains. In documented incidents, the group has exfiltrated victim data in as little as two hours from initial access—a timeline that leaves security teams with virtually no opportunity to detect and respond. This velocity is achieved through Akira’s focus on compromising virtual infrastructure early in the attack lifecycle, allowing them to gain control of VM storage and hypervisor platforms that can disrupt multiple critical systems simultaneously.
Initially focused on VMware ESXi and Microsoft Hyper-V environments, Akira has continuously expanded its capabilities. In a June 2025 attack, the group demonstrated a significant evolution by encrypting Nutanix AHV virtual machine disk files for the first time, exploiting SonicWall vulnerability CVE-2024-40766 to expand beyond its traditional target platforms.
SonicWall VPN Campaign
One of Akira’s most successful campaigns throughout 2025 has involved the systematic targeting of SonicWall SSL VPN devices. Beginning in July 2025, security researchers observed a dramatic increase in Akira activity targeting organizations with SonicWall appliances, potentially exploiting CVE-2024-40766. Arctic Wolf Labs documented that even patched SonicWall devices showed signs of compromise, suggesting the group may have access to additional, undisclosed vulnerabilities or sophisticated bypass techniques.
The campaign’s success led to CISA and international partners issuing updated guidance on November 13, 2025, warning that Akira presents an “imminent threat” to critical infrastructure. In the past 90 days leading up to mid-November, 149 victims have been linked to Akira attacks, with Sophos X-Ops providing incident response support for numerous cases.
Advanced TTPs and Tooling
Akira’s technical sophistication extends across the entire attack lifecycle. The group leverages multiple sophisticated tools including:
- POORTRY malware: Deployed to modify Bring Your Own Vulnerable Driver (BYOVD) configurations, create administrator accounts, steal credentials, and bypass VMDK protections
- SystemBC and STONETOP: Remote access trojans for command and control and payload delivery
- Cobalt Strike: For lateral movement and network reconnaissance
- Remote management tools: AnyDesk and LogMeIn to maintain persistence while mimicking legitimate administrator activity
The group’s defense evasion techniques are equally sophisticated, including modifying firewall settings, terminating antivirus processes, uninstalling EDR systems, and exploiting vulnerabilities in Veeam Backup and Replication to compromise recovery infrastructure.
Akira_v2 Variant
In late 2025, Akira introduced an updated ransomware variant, Akira_v2, featuring faster encryption capabilities and enhanced evasion techniques. The new version represents a continuous evolution of the group’s technical capabilities, incorporating lessons learned from thousands of previous attacks. Security researchers note that Akira threat actors are associated with multiple overlapping groups including Storm-1567, Howling Scorpius, Punk Spider, and Gold Sahara, and may have connections to the defunct Conti ransomware operation.
DragonForce: The Ransomware Cartel
DragonForce represents one of the most intriguing developments in the 2025 ransomware landscape—a hybrid operation that blurs the lines between hacktivism and financial cybercrime while pioneering new business models for affiliate recruitment and operations.
Origins and Evolution
DragonForce first emerged in December 2023 with the launch of its “DragonLeaks” dark web portal. Some researchers trace its lineage to DragonForce Malaysia, a long-standing hacktivist collective, though this connection remains unconfirmed and the hacktivist group denies involvement in ransomware activities. Regardless of its origins, by 2025 DragonForce has evolved into a sophisticated RaaS operation with a unique organizational structure.
Comparing the Biggest CCO/DPO Fines to the Biggest Ransomware Attacks and Cyber Attack DamagesWhile fines for non-compliance with data protection laws such as GDPR and CCPA can reach staggering amounts, the financial damages resulting from ransomware attacks and cyberattacks can sometimes far exceed these fines. Here’s a comparison of the biggest CCO/DPO-related fines with some of the most significant ransomware attacks![]() Breached CompanyBreached Company
Breached CompanyBreached Company
White-Label Ransomware Platform
DragonForce’s technical platform offers affiliates unprecedented customization capabilities. The white-label model allows affiliates to:
- Create unique ransomware brands using DragonForce’s infrastructure
- Compile custom binaries with personalized configurations
- Design custom ransom notes and file extensions
- Access pre-built negotiation tools and encrypted storage
- Utilize templated leak sites branded as “RansomBay”
The commission structure is highly competitive, with DragonForce taking only a 20% revenue share—significantly lower than most RaaS platforms. This aggressive pricing, combined with the platform’s flexibility, proved particularly attractive following RansomHub’s collapse in April 2025, when DragonForce successfully recruited numerous displaced affiliates.
Data Audit Services: A New Monetization Model
In August 2025, DragonForce introduced an innovation that may reshape ransomware economics: data audit services. This offering provides affiliates with detailed analysis of stolen data to maximize extortion leverage. When affiliates submit datasets over 300GB from companies with annual revenues exceeding $15 million, DragonForce’s team analyzes the data and identifies the most valuable commercial and financial information, accompanied by customized extortion letters designed to maximize pressure.
The Royal Mail Ransomware Attack: A Deep Dive into the January 2023 Belfast IncidentIn the ever-evolving landscape of cyber threats, ransomware attacks have emerged as one of the most formidable challenges for organizations worldwide. The beginning of 2023 was no exception, as the UK’s postal service giant, Royal Mail, fell victim to a significant ransomware attack. This incident, which took place in early![]() Breached CompanyBreached Company
Breached CompanyBreached Company
UK Retail Campaign
DragonForce gained significant notoriety in April and May 2025 through a coordinated campaign targeting major UK retailers. The attacks against Marks & Spencer, Harrods, and Co-op triggered multi-day outages of e-commerce platforms, loyalty programs, and internal operations.
The M&S breach was particularly severe, forcing the company to pause all online clothing and home orders for approximately one week, with even in-store contactless payment systems affected. The Cyber Monitoring Centre classified these attacks as a “single combined cyber event” with total losses between £270-440 million ($363-592 million). In July 2025, UK’s National Crime Agency arrested four individuals, including a 17-year-old, in connection with these devastating attacks.
The Co-op incident, though potentially contained before full deployment, revealed the threat actors’ advanced social engineering capabilities. The retailer’s decisive action to “yank their own plug” when they discovered the attack in progress prevented ransomware encryption, though the attack still cost at least £206 million in lost revenues.
Security experts linked these attacks to affiliates using Scattered Spider techniques—sophisticated social engineering combined with DragonForce’s ransomware payload. The attacks represented one of the most devastating waves to hit the UK retail sector.
Aggressive Competition
DragonForce has distinguished itself through openly hostile behavior toward competing ransomware operations. Within 24 hours of announcing its cartel model in March 2025, the group defaced the leak sites of rival operations BlackLock and Mamona. When RansomHub’s infrastructure went offline on April 1, 2025, DragonForce immediately published announcements suggesting RansomHub should join their platform—a move interpreted as both mockery and aggressive recruitment.
UK Bans Ransomware Payments: A New Era in Fighting Cyber ExtortionBottom Line Up Front: The UK has officially banned public sector organizations and critical infrastructure operators from paying ransomware demands, marking a historic shift in cybersecurity policy. While this bold move aims to disrupt criminal business models, ransomware groups are escalating to multi-layered extortion tactics that go far beyond simple![]() Breached CompanyBreached Company
Breached CompanyBreached Company
Other Active RaaS Groups in Late 2025
The fragmentation of the ransomware landscape has created opportunities for numerous other groups to establish themselves as significant threats:
Play Ransomware
Play emerged quietly in 2022 but made a notable leap in 2024 with 369 disclosed victims. The group distinguishes itself through operational execution rather than media theatrics, with victim disclosures designed to apply direct pressure rather than attract attention. Play operates with a solid infrastructure and well-established affiliate network, and notably appears to enforce an internal policy against attacking healthcare institutions—a rare ethical boundary in the ransomware ecosystem.
According to joint advisories from the FBI, CISA, and Australia’s ASD ACSC, Play ransomware has compromised approximately 900 organizations since the group emerged in 2022. The group demonstrated technical sophistication in April 2025 by exploiting a Windows vulnerability (CVE-2025-29824) as a zero-day targeting organizations in the United States, affecting the Windows Common Log File System (CLFS) driver to gain SYSTEM privileges.
Most recently in November 2025, Play ransomware hit Super Quik gas stations, a multi-state convenience store chain, leaking approximately 5.5 GB of internal documents and security camera footage after the company refused to pay ransom demands. Play’s signature techniques include intermittent encryption and exploitation of FortiOS vulnerabilities, with each ransomware binary recompiled for individual campaigns to evade detection.
RansomHub (Defunct)
Once dominant in early 2025, RansomHub’s sudden disappearance in April marked a significant turning point in the year’s ransomware landscape. The platform had attracted affiliates from established groups like ALPHV and LockBit following law enforcement disruptions, and operated with an aggressive profit-sharing model offering affiliates up to 90% of ransom payments. RansomHub’s infrastructure going offline triggered massive affiliate migration to platforms like Qilin and DragonForce. While spokesperson “koley” later claimed the group suffered a state-sponsored attack, RansomHub has not successfully relaunched as of November 2025.
Cl0p (Clop)
Cl0p remains a persistent and sophisticated threat, having evolved from traditional encryption to focus primarily on mass data exfiltration. The Russian-speaking group has generated over $500 million in estimated earnings through systematic exploitation of zero-day vulnerabilities in enterprise file transfer software. In early 2025, Cl0p made an astonishing 345 leak site posts in February alone and 413 for Q1 overall, primarily from drip-fed leaks related to exploitation of vulnerabilities in Cleo’s file transfer software. The group specializes in supply chain attacks, with previous campaigns like the MOVEit Transfer exploitation compromising hundreds of organizations simultaneously.
BlackSuit (Disrupted)
BlackSuit, which emerged as a rebrand of Royal ransomware in 2023, was successfully dismantled through Operation Checkmate in July-August 2025. The operation, coordinating international law enforcement from multiple countries, seized four servers and nine domains used by the group. BlackSuit had compromised over 450 victims since 2022 and extracted more than $370 million in cryptocurrency payments. The group’s sophisticated tactics included partial encryption capabilities and ransom demands ranging from $1 million to $60 million.
8Base
8Base utilizes a branch of the Phobos ransomware that previously made millions from attacks on government and critical infrastructure. The group was one of the standout performers among new RaaS operations emerging in 2023. In February 2025, international law enforcement arrested four Russian nationals leading the 8Base ransomware group in Thailand, taking down their dark web data leak and negotiation sites. Despite this disruption, 8Base maintained some activity early in the year before ceasing operations in Q2 2025 along with several other groups including BianLian, Cactus, and Hunters International.
INC Ransom
INC Ransom focuses on Germany and high-revenue companies, demonstrating geographic targeting preferences. The group has been observed listing healthcare providers among its victims, disregarding informal ethical boundaries observed by some larger RaaS brands.
Medusa
Medusa has experienced periods of significant activity throughout 2025, operating a traditional RaaS model with competitive affiliate terms. Since emerging in 2021, Medusa has evolved into one of the most prolific cybercrime groups targeting critical infrastructure, with a disturbing pattern of attacking healthcare providers and medical imaging facilities.
In October 2025, Medusa claimed responsibility for a massive attack on SimonMed Imaging, one of the largest outpatient medical imaging providers in the United States. The January 2025 attack compromised the protected health information of 1,275,669 individuals, with attackers maintaining network access for 16 days. Medusa demanded $1 million with an additional $10,000 charge for each day’s extension before publishing stolen files.
The group’s targeting of healthcare demonstrates sophisticated sector specialization, with victims including multiple imaging centers, diagnostic facilities, and medical providers. Medusa’s tactics include recruiting insiders, with BBC cyber correspondent Joe Tidy revealing in September 2025 that the gang directly targeted him for recruitment, offering up to 25% of potential multi-million-dollar ransoms. Medusa operates on a double-extortion model, publicly posting proof-of-breach data on their dark web portal when ransom demands are not met.
Fog Ransomware
Fog emerged as a notable threat through systematic exploitation of compromised SonicWall VPN accounts, with Arctic Wolf documenting at least 30 intrusions attributed to the group. Notably, 75% of these intrusions showed connections to Akira infrastructure, suggesting shared resources or collaboration. Fog demonstrated alarming speed, with the shortest observed time from initial access to encryption being just two hours. The group primarily targets education, business services, travel, and manufacturing sectors, with a particular focus on educational institutions—unusual among ransomware operators.
Lynx
Lynx operates as a double-extortion ransomware group that has been very active in 2024-2025, displaying numerous victimized companies on its website. The group encrypts files with a ”.LYNX” extension and places “README.txt” ransom notes in multiple directories. In 2024 alone, Lynx claimed more than 70 victims, demonstrating continued activity and growing presence.
KillSec (Kill Security)
Active for approximately one year, KillSec has recently gained attention through steady victim disclosures and promotion of its RaaS model and additional services. The group represents the newer generation of ransomware operations seeking to establish market presence through consistent activity and professional infrastructure.
Anubis
A new RaaS group active since at least November 2024, Anubis has focused strongly on data extortion, potentially redefining double extortion into what security researchers describe as “malevolence as a service.” The group’s approach emphasizes psychological pressure and sophisticated extortion tactics beyond simple data theft and encryption.
Sarcoma
Sarcoma has been identified by Halcyon researchers as one of the top emerging threat groups to watch in 2025. While details remain limited, the group’s inclusion in threat intelligence reports suggests growing capabilities and activity levels.
Cicada3301
Cicada3301 appears to have elite RaaS operator heritage, though the group currently focuses on small and medium-sized businesses rather than big-game hunting. Security researchers anticipate the group will become significantly more ambitious, given its technical capabilities and operator experience. Initial compromise appears to primarily occur through Remote Desktop Protocol using stolen or weak credentials.
The RaaS Business Model: How It Works
Understanding the current threat landscape requires examining how RaaS platforms operate as businesses:
Revenue Structures
RaaS platforms employ various pricing models:
- Profit sharing: The most common model, with splits ranging from 70/30 to 85/15 in favor of affiliates
- Subscription fees: Monthly or quarterly payments for access to ransomware infrastructure
- One-time licensing: Less common in 2025, as most groups prefer recurring revenue
- Hybrid models: Combining upfront fees with profit sharing
Services Provided
Professional RaaS platforms offer comprehensive services:
- Ransomware development and maintenance
- Regular updates to evade detection
- Customizable payloads for different environments
- Negotiation platforms and secure communications
- Leak sites for data extortion
- Payment processing through cryptocurrency
- 24/7 affiliate support
- Tutorial documentation and training
- Data hosting for exfiltrated files
Recruitment and Vetting
Most RaaS platforms actively recruit on underground forums like RAMP and XSS, advertising their technical advantages, successful track record, and generous affiliate terms. Some platforms implement vetting processes to ensure affiliates have the technical skills to successfully execute attacks, though standards vary widely across operations.
Infrastructure and Tools
RaaS platforms provide affiliates with sophisticated tools:
- Admin and client dashboards
- Encryption and decryption utilities
- Data exfiltration tools (often integrating with cloud services like MEGA)
- Network scanning and reconnaissance tools
- Credential harvesting utilities (Mimikatz, Cobalt Strike)
- Remote access tools for persistence
- Defense evasion scripts
- Automated victim tracking and leak site management
Evolving Tactics and Techniques
The ransomware threat landscape in late 2025 is characterized by several key tactical trends:
Double and Triple Extortion
Double extortion—combining encryption with data theft threats—has become standard, occurring in approximately 95% of incidents. Some groups have evolved to triple extortion, adding DDoS attacks or threats to notify customers and partners about breaches, multiplying pressure on victims.
Data-First Attacks
An increasing number of operations have abandoned encryption entirely in favor of pure data exfiltration and extortion. This approach reduces operational complexity, eliminates the risk of faulty decryption tools, and accelerates the attack timeline. Groups like World Leaks (formerly Hunter’s International) specialize in this approach, which some researchers describe as a shift from ransomware to “pure extortion.”
Supply Chain Targeting
Ransomware groups increasingly target managed service providers, software vendors, and cloud platforms to gain access to multiple downstream victims simultaneously. The CDK Global attack in June 2024, which crippled approximately 15,000 auto dealerships, exemplifies this approach’s devastating potential.
Similarly, in September 2025, a ransomware attack on Collins Aerospace’s passenger processing system disrupted operations at several major European airports including Heathrow, Brussels, and Berlin. The HardBit ransomware attack on Collins’ MUSE software caused multi-day outages and forced manual check-in procedures. Security experts noted that Collins Aerospace had previously been targeted by the BianLian ransomware group in 2023, raising concerns that backdoors from the earlier breach may have facilitated the recent attack—though BianLian ceased operations in March 2025.
Dublin Airport Data Breach Exposes 3.8 Million Passengers in Collins Aerospace HackBreaking: Third-Party Supplier Breach Compromises Boarding Pass Data for Entire Month of August 2025 October 26, 2025 - Dublin Airport has confirmed a significant data breach affecting potentially all 3.8 million passengers who traveled through the Irish capital’s terminals during August 2025, following a cyberattack on aviation technology supplier![]() Breached CompanyBreached Company
Breached CompanyBreached Company Other 2025 supply chain attacks include exploitation of file transfer software like MOVEit, Cleo, and SonicWall, providing access to hundreds or thousands of organizations through single compromises. The aviation sector specifically saw a 600% increase in cyber-attacks between 2024 and 2025, with 27 documented ransomware attacks involving 22 different groups.
Other 2025 supply chain attacks include exploitation of file transfer software like MOVEit, Cleo, and SonicWall, providing access to hundreds or thousands of organizations through single compromises. The aviation sector specifically saw a 600% increase in cyber-attacks between 2024 and 2025, with 27 documented ransomware attacks involving 22 different groups.
AI Integration
Several groups have begun integrating artificial intelligence tools into their operations:
- FunkSec openly uses LLMs for phishing template generation and developed the malicious chatbot WormGPT
- DragonForce offers AI-enhanced data analysis services
- Various groups use AI for automated vulnerability scanning, social engineering content generation, and network reconnaissance
Credential Access Brokers
The ransomware ecosystem increasingly relies on initial access brokers (IABs) who specialize in compromising networks and selling access to RaaS affiliates. This division of labor allows affiliates to focus on data exfiltration and encryption while IABs handle the technically challenging initial compromise.
BYOVD Attacks
Bring Your Own Vulnerable Driver attacks have become common, with groups deploying legitimate but vulnerable drivers to disable security software and evade detection. This technique allows ransomware operators to gain kernel-level access and terminate security processes that would otherwise detect and block their activities.
Geographic and Sectoral Targeting
Geographic Distribution
The United States continues to bear the brunt of ransomware attacks, accounting for approximately 50% of global victims throughout 2025. Other heavily targeted regions include:
- United Kingdom
- Canada
- Germany
- France
- Australia
- South Korea (particularly for Qilin’s financial sector campaign)
Sector Analysis
Manufacturing remains the most targeted sector, representing about 23% of attacks in recent analysis. Other heavily impacted sectors include:
- Business services (11%)
- Healthcare (8-10%)
- Construction (10%)
- Financial services
- Education
- Government/public sector
- Professional and scientific services (18% for Qilin specifically)
- Wholesale trade (10%)
- Technology
Healthcare presents a particularly concerning target due to the life-or-death nature of medical services. While some groups like Play ransomware appear to avoid healthcare targeting due to the attention such attacks attract, others including Qilin, INC Ransom, and KillSec continue listing healthcare providers among their victims.
Municipal and state governments have experienced devastating attacks throughout 2025, with Nevada suffering an unprecedented statewide shutdown in August 2025 that forced DMV closures and crippled state agency operations for days. St. Paul, Minnesota’s attack was severe enough to trigger National Guard deployment. Between 2018 and 2024, there were 525 individual ransomware attacks against U.S. municipalities and government organizations, with estimated costs exceeding $52.88 billion over the past three years.
Law Enforcement Response and Challenges
Despite significant law enforcement successes including Operation Cronos (LockBit), Operation Checkmate (BlackSuit), and various ALPHV/BlackCat disruptions, the overall volume of ransomware attacks has remained stable or increased. This resilience stems from several factors:
Affiliate Migration
Law enforcement operations primarily target infrastructure and core group operators but rarely capture affiliates, who are the actual attackers in the RaaS model. When a platform is disrupted, affiliates simply migrate to alternative operations, often within days or weeks. The swift movement of affiliates from RansomHub to Qilin and DragonForce in April-May 2025 exemplifies this pattern.
A particularly troubling example emerged in October 2025 when three former cybersecurity incident response professionals were indicted for operating as ALPHV BlackCat affiliates. Between May 2023 and April 2025, the defendants allegedly systematically targeted companies across multiple states, exploiting their insider knowledge of victim vulnerabilities and negotiation tactics. As of September 2023, ALPHV BlackCat affiliates had compromised over 1,000 entities, demanding over $500 million and receiving nearly $300 million in ransom payments.
Rapid Rebranding
Ransomware groups frequently rebrand following law enforcement action, reemerging under new names with similar infrastructure and personnel. The evolution from Royal to BlackSuit, and suspected connections between various operations, demonstrates how groups maintain operational continuity despite disruptions.
Jurisdictional Challenges
Most major ransomware operations originate from Russia or CIS countries where U.S. and European law enforcement have limited reach. Russian-language threat actors also benefit from apparent tolerance by Russian authorities, provided they avoid targeting Russian or CIS victims—a principle demonstrated by the geographic avoidance patterns programmed into most major ransomware variants.
Technical Sophistication
Modern ransomware operations employ sophisticated operational security:
- Tor-based infrastructure
- Cryptocurrency payment processing
- Encrypted communications
- Virtual private servers in multiple jurisdictions
- Money laundering through cryptocurrency tumblers and exchanges
- Anonymous recruitment and vetting processes
Advanced threat groups like Scattered Spider have evolved beyond traditional ransomware tactics, actively fighting back against incident response teams, countering security moves in real-time, and sabotaging eviction attempts. These sophisticated adversaries view incident response as just another obstacle to overcome, requiring organizations to fundamentally rethink their defense strategies beyond passive protection measures.
Collaboration Improvements
Despite these challenges, international law enforcement has demonstrated increasing sophistication in coordinating cross-border operations. Recent actions have involved partnerships between U.S. agencies (FBI, CISA, Secret Service), European authorities (Europol, national police forces), and agencies from Australia, Canada, and Asia-Pacific countries. These collaborations have successfully seized infrastructure, sanctioned operators, and recovered ransom payments.
Economic Impact and Ransom Payments
The economic impact of ransomware in 2025 has reached unprecedented levels:
Payment Trends
Ransom demands typically range from hundreds of thousands to tens of millions of dollars, with reported demands including:
- Akira: Typical demands from $200,000 to several million
- Qilin: $50 million demanded from Synnovis Laboratories
- BlackSuit: Demands ranging from $1 million to $10 million, with the highest recorded demand reaching $60 million
- Cl0p: Multiple campaigns generating over $500 million in total proceeds
The average payment rate has been declining as organizations improve defenses and backup capabilities, though precise figures vary by sector and incident. However, total annual ransomware proceeds likely exceed $1 billion globally, with some estimates suggesting significantly higher figures when unreported incidents are included.
Recovery Costs
Beyond ransom payments, organizations face substantial recovery costs:
- According to Sophos, the average cost to recover from an attack (excluding ransom) was $1.53 million in 2025, down 44% from previous years
- Extended downtime and operational disruption
- Legal and regulatory penalties under GDPR, HIPAA, and other frameworks
- Credit monitoring for affected individuals
- Reputational damage and customer loss
- Enhanced security investments post-incident
Insurance Considerations
The cyber insurance market has adapted to the ransomware threat with increased premiums, more stringent underwriting requirements, and in some cases, reluctance to cover ransom payments. Some jurisdictions are considering regulations that would prohibit or restrict ransom payments to disrupt the criminal business model.
Defense Strategies and Mitigation
Organizations facing this threat landscape should implement comprehensive defense strategies:
Prevention
Access Control:
- Implement phishing-resistant multifactor authentication universally
- Enforce principle of least privilege
- Regularly audit and remove unnecessary accounts
- Use strong, unique passwords managed through enterprise password management
Vulnerability Management:
- Prioritize patching of known exploited vulnerabilities
- Implement vulnerability scanning and management programs
- Pay special attention to edge devices (VPNs, firewalls, remote access solutions)
- Consider virtual patching for systems that cannot be immediately updated
Network Segmentation:
- Segment critical systems and data
- Implement zero-trust architecture principles
- Restrict lateral movement capabilities
- Monitor east-west traffic, not just north-south
Email and Endpoint Security:
- Deploy advanced email filtering and anti-phishing solutions
- Implement endpoint detection and response (EDR)
- Enable and properly configure built-in security features
- Regularly test security controls
Detection
Security Monitoring:
- Implement 24/7 security monitoring through SOC or MDR services
- Deploy SIEM solutions with appropriate use cases
- Monitor for unusual data transfers and encryption activities
- Track authentication attempts and privileged account usage
Threat Intelligence:
- Subscribe to threat intelligence services focused on ransomware TTPs
- Monitor for compromised credentials on dark web markets
- Participate in information sharing organizations (ISACs)
- Track ransomware group activities and leaked indicators
Response
Incident Response Planning:
- Develop and regularly test incident response plans
- Conduct tabletop exercises for ransomware scenarios
- Identify key team members and establish communication procedures
- Define decision-making processes for ransom payment considerations
Backup and Recovery:
- Maintain regular backups of critical data
- Store backups offline or in immutable storage
- Regularly test restoration processes
- Implement the 3-2-1 backup rule (3 copies, 2 different media, 1 offsite)
Communication Strategies:
- Prepare communication templates for various stakeholders
- Establish relationships with law enforcement before incidents occur
- Consider cyber insurance to offset costs and access expert resources
- Understand regulatory notification requirements
The Future of Ransomware
As we look toward 2026 and beyond, several trends appear likely to shape the ransomware landscape:
Continued Fragmentation
The decentralization of ransomware operations will likely continue, with smaller, more agile groups competing alongside surviving major platforms. This fragmentation makes the threat environment more complex and unpredictable while potentially reducing the impact of any single law enforcement operation.
Advanced Evasion
Ransomware developers will continue innovating to evade detection, incorporating:
- More sophisticated encryption algorithms
- Enhanced anti-analysis capabilities
- Living-off-the-land techniques using legitimate tools
- AI-powered attack automation and optimization
Hybrid Threats
The line between state-sponsored operations and financially motivated cybercrime will continue blurring. Operations like Storm-2603’s Warlock ransomware demonstrate how nation-state capabilities can be deployed for apparent financial gain, creating complex attribution challenges and policy complications.
Regulatory Evolution
Governments worldwide are implementing stricter cybersecurity requirements and incident reporting mandates. The EU’s NIS2 Directive and Digital Operational Resilience Act (DORA), along with U.S. regulations like SEC’s 4-day disclosure rule and CISA’s 72-hour CIRCIA reporting requirement, will force greater transparency and accountability.
Payment Controversies
Debate continues around whether paying ransoms should be prohibited or restricted. Some argue that prohibition would reduce criminal profitability and incentivize better security practices. Others contend that such bans would merely drive payment activity underground while leaving victims in desperate situations without recourse. This policy debate will likely intensify as attack volumes remain elevated.
Conclusion
The Ransomware-as-a-Service ecosystem in late 2025 represents a mature, industrialized form of cybercrime that shows no signs of abating despite significant law enforcement successes. The disruption of LockBit—once the industry’s dominant player—failed to reduce overall attack volumes and instead triggered a competitive free-for-all among groups like Qilin, Akira, and DragonForce, each innovating to attract displaced affiliates and establish market dominance.
Qilin has emerged as the current leader through generous affiliate terms, sophisticated technical capabilities, and aggressive recruitment following competitor disruptions. Akira distinguishes itself through remarkable attack speed and systematic targeting of virtual infrastructure and VPN appliances. DragonForce has pioneered new business models with its cartel approach, white-label platform, and data audit services, while demonstrating that hybrid operations blending multiple criminal activities may represent the future of organized cybercrime.
The proliferation of smaller operations, the fragmentation of the threat landscape, and the integration of artificial intelligence into attack chains all point to an increasingly complex and dangerous environment. Organizations can no longer rely on the assumption that only the largest enterprises face ransomware risk—the democratization of attack capabilities through RaaS platforms means that any organization with valuable data or critical operations is a potential target.
Success in this environment requires a comprehensive approach combining prevention, detection, and response capabilities. Organizations must implement defense-in-depth strategies, maintain viable backup and recovery capabilities, and prepare incident response plans before attacks occur. The ransomware threat will remain a defining challenge of the cyber landscape for the foreseeable future, demanding sustained vigilance, investment, and adaptation from defenders worldwide.
For more information on ransomware threats and cybersecurity best practices, visit breached.company for in-depth analysis, recent incident reports, and comprehensive threat intelligence.