Nation-State Actors Turn Blockchain Into an Indestructible Malware Platform
Executive Summary: In a watershed moment for cybersecurity, North Korean state-sponsored hackers have begun embedding malware directly into blockchain smart contracts, creating a decentralized, nearly indestructible command-and-control infrastructure. This technique, called “EtherHiding,” represents a fundamental shift in how malware is distributed and managed—transforming the very properties that make blockchain revolutionary into weapons for cyber espionage and financial crime.
The $1.37 Malware Update That Changes Everything
For just $1.37 in blockchain transaction fees, North Korean hackers can now update their malware payload and distribute it to victims worldwide. This isn’t just another cybersecurity threat—it’s a paradigm shift that transforms decentralized technology into what researchers call “next-generation bulletproof hosting.”
Google Threat Intelligence Group has identified the North Korea-linked threat actor UNC5342 as using EtherHiding to deliver malware and facilitate cryptocurrency theft, marking the first time a nation-state actor has adopted this method. The campaign, active since February 2025, has already led to numerous cryptocurrency heists and represents a troubling evolution in state-sponsored cyber operations.
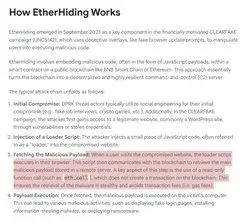



What Is EtherHiding?
EtherHiding involves embedding malicious code within smart contracts on public blockchains like BNB Smart Chain or Ethereum, essentially turning the blockchain into a decentralized and highly resilient command-and-control server.
Unlike traditional malware infrastructure that can be seized by law enforcement or blocked by cybersecurity firms, blockchain-based malware offers attackers four critical advantages:
1. Decentralization and Resilience Because malicious code is stored on a decentralized and permissionless blockchain, there is no central server that law enforcement can take down. The malicious code remains accessible as long as the blockchain itself is operational.
2. Anonymity The pseudonymous nature of blockchain transactions makes it difficult to trace the identity of attackers who deployed the smart contract.
3. Immutability Once deployed to the blockchain, the malicious smart contract becomes a permanent fixture that cannot be easily removed or altered by anyone except the contract owner.
4. Flexibility and Stealth Attackers can retrieve malicious payloads using read-only calls that do not leave visible transaction history on the blockchain, making their activities harder to track. The attacker who controls the smart contract can update the malicious payload at any time.
The Contagious Interview: Social Engineering Meets Blockchain
The attack vector is as sophisticated as the technology behind it. North Korean threat actors create convincing but fraudulent profiles on professional networking sites like LinkedIn and job boards, often impersonating recruiters from well-known tech or cryptocurrency firms.
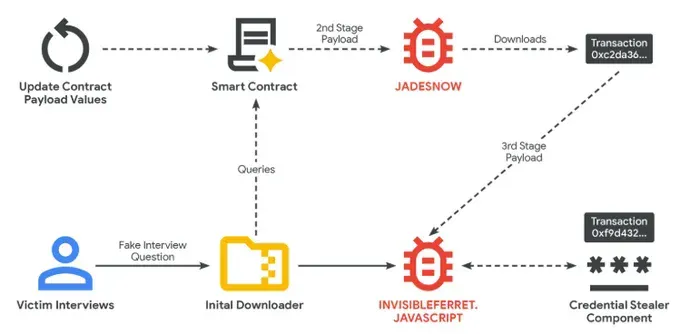
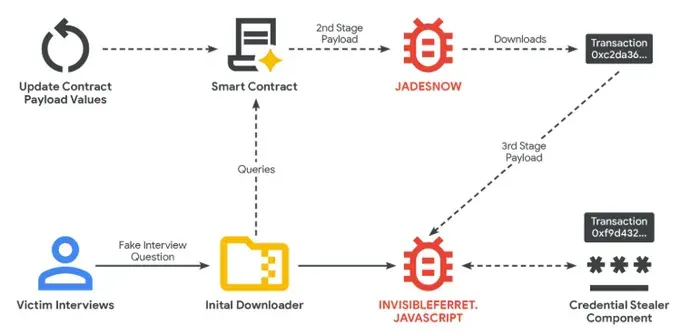
The attack unfolds in several carefully orchestrated stages:
Phase 1: The Lure
Fake recruiters approach developers, particularly those working in cryptocurrency and technology sectors, with attractive job offers. They often move conversations to platforms like Telegram or Discord.
Phase 2: The Trojan Horse
During a technical assessment phase, candidates are asked to perform a coding test or review a project, which requires them to download files from repositories like GitHub. These files contain malicious code.
Phase 3: The Infection Chain
Once executed, the malware initiates a multi-stage infection process targeting Windows, macOS, and Linux systems:
- JADESNOW: A JavaScript-based downloader that queries blockchain smart contracts to retrieve the next stage payload
- BEAVERTAIL: A credential stealer focused on cryptocurrency wallets, browser extensions, and sensitive data
- INVISIBLEFERRET: A sophisticated JavaScript backdoor providing remote control and long-term access to compromised systems
The Technical Deep Dive: How the Blockchain Attack Works
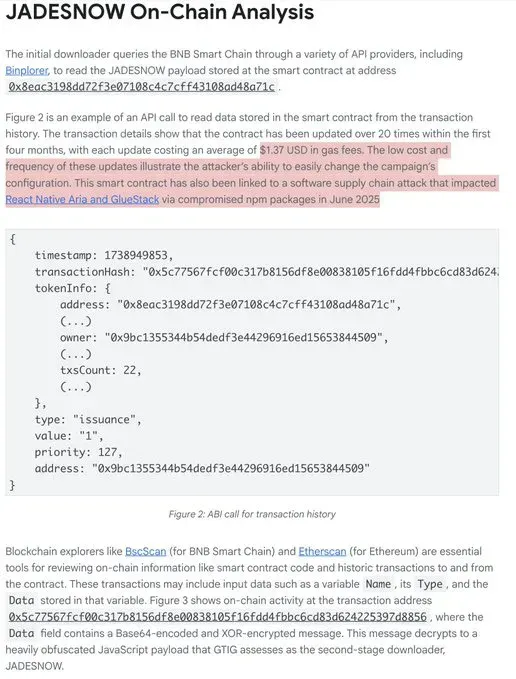
The initial downloader queries the BNB Smart Chain through various API providers to read the JADESNOW payload stored in smart contracts. In one analyzed case, the transaction details showed the contract had been updated over 20 times within the first four months, with each update costing an average of $1.37 USD in gas fees.
What makes this attack particularly sophisticated is UNC5342’s use of multiple blockchains within a single operation. It is unusual to see a threat actor make use of multiple blockchains for EtherHiding activity; this may indicate operational compartmentalization between teams of North Korean cyber operators.
The malware can switch between Ethereum and BNB Smart Chain, complicating analysis and leveraging lower transaction fees offered by alternate networks.
The Clever Dead Drop Resolver
Rather than storing all malicious code in smart contracts, the attackers have developed an even stealthier approach. They perform GET requests to query transaction history of attacker-controlled addresses and read data stored from transactions made to the well-known “burn” address, effectively using blockchain transactions as a Dead Drop Resolver.
This means the malware simply reads transaction data rather than executing smart contract functions, making detection even more challenging.
The Dual Purpose: Espionage and Financial Crime
North Korea’s adoption of EtherHiding serves the regime’s twin strategic objectives:
Financial Gain North Korean hackers stole over $1.3 billion across 47 incidents in 2024 and $2.2 billion in the first half of 2025 alone, funding the regime’s weapons program through elaborate money laundering networks.
Cyber Espionage By compromising developers at technology companies, North Korea gains intelligence and establishes footholds for future operations. For high-value targets, a persistent backdoor provides remote control over compromised systems, allowing for long-term espionage and lateral movement within networks.
The Frightening Evolution: What Comes Next?
Security researchers are already warning about the next phase of blockchain-based attacks. As one expert noted in recent analysis, we should expect attackers to experiment with directly loading zero-click exploits onto blockchains, targeting systems and applications that process blockchain data—especially if hosted on the same systems that handle cryptocurrency transactions or store wallets.
The implications are staggering:
The Zero-Click Blockchain Threat
Zero-click exploits bypass user awareness entirely. A single malicious image or file could grant attackers full control over a device, enabling irreversible transactions or exfiltration of private keys.
If attackers successfully embed zero-click exploits in blockchain smart contracts, they could potentially compromise:
- Blockchain explorers and analysis tools
- Cryptocurrency wallet applications
- DeFi platforms and exchanges
- Development environments where blockchain code is tested
The Agentic AI Wild Card
The convergence of agentic AI, low-skill “vibe coding,” and blockchain-based malware creates a perfect storm. Developers increasingly use AI coding assistants on the same machines where they store cryptocurrency wallets. This practice, combined with blockchain-based malware that can persist indefinitely, represents what one researcher called “a gold seam that is going to be productive for a long time.”
Blockchain Explorers: The Next Natural Target
Platforms like BscScan, Etherscan, and other blockchain explorers process enormous amounts of data and are used by millions of cryptocurrency users. Blockchain explorers are essential tools for reviewing on-chain information like smart contract code and historic transactions. These platforms represent high-value targets for attackers looking to compromise large numbers of users simultaneously.
The Ironic Weakness: Centralization
Despite leveraging decentralized technology, the attack contains a critical vulnerability. Neither UNC5342 nor other threat actors are interacting directly with blockchains when retrieving information from smart contracts; both are utilizing centralized services like API providers and blockchain explorers.
These centralized intermediaries represent points of observation and control, where traffic can be monitored and malicious activity can be addressed through blocking, account suspensions, or other methods.
However, the report notes a troubling reality: When contacted by Google Threat Intelligence Group, responsible API service providers were quick to take action against this malicious activity; however, several other platforms have remained unresponsive. This indifference and lack of collaboration is a significant concern, as it increases the risk of this technique proliferating among threat actors.
Defensive Strategies: How Organizations Can Protect Themselves
For Individuals and Developers
1. Scrutinize Job Offers Be immediately suspicious of recruiters asking you to download and run code, especially during technical assessments. Legitimate companies provide sandboxed environments for coding tests.
2. Isolate Development Environments Never store cryptocurrency wallets or sensitive credentials on machines used for running untrusted code or evaluating third-party software.
3. Verify Recruiter Identities Cross-reference LinkedIn profiles with company websites. Contact companies directly through official channels to verify recruiter identities.
4. Use Hardware Wallets Store cryptocurrency in hardware wallets that remain offline and are only connected when needed for specific transactions.
For Organizations
1. Implement Browser-Level Controls Chrome Enterprise can prevent EtherHiding attacks by blocking downloads of dangerous file types like .exe, .msi, .bat, and .dll through the DownloadRestrictions policy.
2. Centralize Update Management Chrome Enterprise allows administrators to control and automate browser updates, pushing them silently in the background. Employees can be trained with a simple message: “You will never be asked to manually update Chrome.”
3. Network-Level Monitoring Monitor traffic to blockchain API providers and explorers. Establish baselines for normal blockchain interaction patterns and alert on anomalies.
4. Enhanced Endpoint Detection Deploy endpoint detection and response (EDR) solutions capable of identifying suspicious JavaScript execution, especially code that queries blockchain APIs.
5. Security Awareness Training Educate employees about the Contagious Interview campaign and similar social engineering tactics. Make them aware that fake job offers are being used to distribute malware.
For API Providers and Blockchain Platforms
The blockchain ecosystem must accept responsibility for preventing abuse of its infrastructure:
1. Implement Abuse Detection Develop machine learning models to identify suspicious patterns in smart contract deployments and API usage.
2. Rapid Response Protocols Establish clear processes for responding to reports of malicious smart contracts and suspicious API usage.
3. Collaborative Threat Intelligence Share indicators of compromise and attack patterns across the blockchain security community.
4. User Warnings Display prominent warnings when users interact with flagged smart contracts, similar to browser phishing warnings.
The Broader Implications: A New Chapter in Cyber Warfare
The adoption of EtherHiding by a nation-state actor represents more than just another attack technique—it signals a fundamental shift in the cyber threat landscape.
The End of Takedowns For decades, cybersecurity defenders and law enforcement have relied on the ability to seize servers, block domains, and disrupt command-and-control infrastructure. Blockchain-based malware makes these traditional approaches obsolete.
The Democratization of Sophisticated Attacks If North Korea is using EtherHiding now, how long before the technique proliferates to ransomware gangs, financially motivated cybercriminals, and hacktivist groups? The low cost and high resilience make it attractive to any threat actor.
The Web3 Security Reckoning EtherHiding marks a new chapter in the convergence of state cyber operations, financial motives, and Web3 infrastructures. The cryptocurrency and blockchain communities must confront the reality that the same properties making their technology revolutionary also make it attractive to adversaries.
The Attribution Challenge The pseudonymous nature of blockchain transactions makes it difficult to trace the identity of attackers. This compounds an already difficult attribution problem in cybersecurity, potentially emboldening more aggressive state-sponsored operations.
The Road Ahead: Adaptation or Exploitation?
We stand at a crossroads. The blockchain ecosystem can either:
Option 1: Adapt Develop robust abuse detection systems, establish industry-wide security standards, and create mechanisms for rapid response to malicious smart contracts—all while preserving the decentralized ethos that makes blockchain valuable.
Option 2: Remain Complacent Continue treating blockchain security as someone else’s problem, watching as EtherHiding proliferates across threat actor groups and becomes the new standard for resilient malware infrastructure.
The choice isn’t just about cryptocurrency exchanges or DeFi platforms. As blockchain technology becomes more integrated into enterprise systems, supply chains, and critical infrastructure, the stakes grow exponentially higher.
Conclusion: The Immutable Threat Demands Immediate Action
North Korea’s adoption of EtherHiding isn’t just another cybersecurity news story—it’s a warning shot across the bow of the entire digital ecosystem. For $1.37 per update, nation-state actors can now deploy malware that is effectively immune to traditional takedown efforts.
EtherHiding represents a shift toward next-generation bulletproof hosting, where the inherent features of blockchain technology are repurposed for malicious ends. This technique underscores the continuous evolution of cyber threats as attackers adapt and leverage new technologies to their advantage.
The question isn’t whether other threat actors will adopt this technique—it’s how quickly they’ll do so and whether defenders can develop effective countermeasures before blockchain-based malware becomes ubiquitous.
The immutable threat is here. The only question is whether our response will be equally resolute.
Indicators of Compromise
Organizations should monitor for the following indicators associated with UNC5342’s EtherHiding campaigns:
Malicious Smart Contracts:
- BNB Smart Chain:
0x8eac3198dd72f3e07108c4c7cff43108ad48a71c
Ethereum Transaction Addresses:
0x86d1a21fd151e344ccc0778fd018c281db9d40b6ccd4bdd3588cb40fade1a33a0xc2da361c40279a4f2f84448791377652f2bf41f06d18f19941a96c720228cd0f0xf9d432745ea15dbc00ff319417af3763f72fcf8a4debedbfceeef4246847ce41
Malware Families:
- JADESNOW (JavaScript downloader)
- BEAVERTAIL (credential stealer)
- INVISIBLEFERRET.JAVASCRIPT (backdoor)
Associated Threat Actor Names:
- UNC5342 (Google/Mandiant)
- CL-STA-0240 (Palo Alto Networks)
- DeceptiveDevelopment (ESET)
- DEV#POPPER (Securonix)
- Famous Chollima (CrowdStrike)
- Gwisin Gang (DTEX)
- Tenacious Pungsan (Datadog)
- Void Dokkaebi (Trend Micro)
Additional Resources
- Google Cloud Blog: DPRK Adopts EtherHiding
- MITRE ATT&CK: Dead Drop Resolver (T1102.001)
- Chrome Enterprise Security Policies
This article was researched and compiled on October 17, 2025. Given the rapidly evolving nature of this threat, readers are encouraged to monitor updates from Google Threat Intelligence Group and other cybersecurity vendors for the latest information.
EtherHiding Technical Reference Sheet
UNC5342 (North Korean) Blockchain Malware Campaign
Last Updated: October 17, 2025 Source: Google Threat Intelligence Group, Mandiant Threat Level: Critical Active Since: February 2025
Threat Actor Profile
Primary Designation: UNC5342
Alternative Names:
- CL-STA-0240 (Palo Alto Networks Unit 42)
- DeceptiveDevelopment (ESET)
- DEV#POPPER (Securonix)
- Famous Chollima (CrowdStrike)
- Gwisin Gang (DTEX)
- Tenacious Pungsan (Datadog)
- Void Dokkaebi (Trend Micro)
Attribution: Democratic People’s Republic of Korea (North Korea)
Motivation:
- Financial gain (cryptocurrency theft)
- Cyber espionage
- Sanctions evasion
Campaign Details
Campaign Name: Contagious Interview Attack Vector: Social engineering via fake job recruiters Initial Contact: LinkedIn, job boards Communication Platforms: Telegram, Discord Target Sectors:
- Cryptocurrency developers
- Technology sector developers
- Blockchain companies
- Web3 projects
Platforms Affected: Windows, macOS, Linux
Malware Families
JADESNOW
Type: JavaScript-based downloader Purpose: Queries blockchain smart contracts to retrieve next-stage payloads Blockchains Used: BNB Smart Chain, Ethereum Retrieval Method: Read-only calls via centralized API providers
YARA Rule:
rule G_Downloader_JADESNOW_1 {
meta:
author = "Google Threat Intelligence Group (GTIG)"
description = "Detects JADESNOW malware"
date = "2025-10"
strings:
$s1 = "global['_V']"
$s2 = "global['r']"
$s3 = "umP"
$s4 = "mergeConfig"
$s5 = "charAt" nocase
condition:
uint16(0) != 0x5A4D and
filesize < 10KB and
#s3 > 2 and
#s5 == 1 and
all of them
}
BEAVERTAIL
Type: JavaScript credential stealer Purpose: Exfiltrates sensitive information Targets:
- Cryptocurrency wallets (MetaMask, Phantom)
- Browser extension data
- Stored credentials
- Session cookies
- Credit card information
INVISIBLEFERRET (JavaScript variant)
Type: Backdoor Purpose: Remote control and long-term access C2 Port: 3306 (MySQL default port - likely for evasion) Capabilities:
-
Arbitrary command execution
-
Directory navigation
-
File/directory exfiltration Credential stealing from:
-
Web browsers (Chrome, Edge)
-
Password managers (1Password)
-
Cryptocurrency wallets
-
Data exfiltration via ZIP archives to attacker servers and Telegram
Initial Beacon Data:
- Victim hostname
- Username
- Operating system
- Current directory
Blockchain Indicators of Compromise
BNB Smart Chain
Malicious Smart Contract Address:
0x8eac3198dd72f3e07108c4c7cff43108ad48a71c
Transaction Example:
0x5c77567fcf00c317b8156df8e00838105f16fdd4fbbc6cd83d624225397d8856
Explorer Links:
- https://bscscan.com/address/0x8eac3198dd72f3e07108c4c7cff43108ad48a71c
- https://bscscan.com/tx/0x5c77567fcf00c317b8156df8e00838105f16fdd4fbbc6cd83d624225397d8856
Update Frequency: 20+ times in first 4 months Average Gas Fee: $1.37 USD per update
Ethereum
Malicious Transaction Addresses:
INVISIBLEFERRET.JAVASCRIPT Payload:
0x86d1a21fd151e344ccc0778fd018c281db9d40b6ccd4bdd3588cb40fade1a33a
Split Payload Components:
0xc2da361c40279a4f2f84448791377652f2bf41f06d18f19941a96c720228cd0f
0xf9d432745ea15dbc00ff319417af3763f72fcf8a4debedbfceeef4246847ce41
Explorer Links:
- https://etherscan.io/tx/0x86d1a21fd151e344ccc0778fd018c281db9d40b6ccd4bdd3588cb40fade1a33a
- https://etherscan.io/tx/0xc2da361c40279a4f2f84448791377652f2bf41f06d18f19941a96c720228cd0f
- https://etherscan.io/tx/0xf9d432745ea15dbc00ff319417af3763f72fcf8a4debedbfceeef4246847ce41
Technique: Dead Drop Resolver - sends transactions to burn address 0x00...dEaD and reads calldata
Network Indicators
Blockchain API Providers Queried
BNB Smart Chain:
- Binplorer (binplorer.com)
- Other BSC API providers (various)
Ethereum:
- Blockchair
- Blockcypher
- Ethplorer (using free API key:
apiKey=freekey) - Multiple explorers queried simultaneously as failsafe
C2 Communication
Port: 3306 (MySQL default) Protocol: Custom Encryption: XOR + Base64 encoding for payloads Exfiltration:
- Direct upload to attacker servers
- Private Telegram chats
Attack Chain Summary
1. Fake LinkedIn Recruiter
↓
2. Move to Telegram/Discord
↓
3. Request coding test/file review
↓
4. Download malicious npm package or GitHub repo
↓
5. Execute initial JavaScript downloader
↓
6. Query BNB Smart Chain → Retrieve JADESNOW
↓
7. JADESNOW queries Ethereum → Retrieve INVISIBLEFERRET
↓
8. INVISIBLEFERRET establishes C2
↓
9. Deploy credential stealer
↓
10. Exfiltrate cryptocurrency wallets, credentials, sensitive data
Detection Strategies
Network-Level Detection
Monitor for suspicious blockchain API queries:
# Example Snort/Suricata rule concept
alert http any any -> any any (
msg:"Possible EtherHiding - Multiple rapid blockchain API queries";
content:"bscscan.com";
content:"etherscan.io";
content:"blockchair.com";
threshold: type both, track by_src, count 10, seconds 60;
classtype:trojan-activity;
)
DNS Queries to Monitor:
- binplorer.com
- bscscan.com
- etherscan.io
- blockchair.com
- blockcypher.com
- ethplorer.io
- API endpoints for BNB Smart Chain and Ethereum
Unusual Port Usage:
- Unexpected connections on port 3306 to non-database servers
Endpoint Detection
Process Monitoring:
- JavaScript/Node.js processes making blockchain API calls
- Processes querying smart contract addresses
- Base64 decoding followed by code execution
- XOR decryption operations in JavaScript
File System Monitoring:
- npm packages with suspicious blockchain interactions
- JavaScript files in unexpected locations
- Portable Python interpreter installations
- ZIP archive creation with cryptocurrency wallet data
Registry/Configuration Changes (Windows):
- Browser extension modifications
- Password manager access attempts
- Cryptocurrency wallet installations
Email/Communication Monitoring
Social Engineering Indicators:
- Unsolicited job offers from cryptocurrency/tech companies
- Requests to move conversation to Telegram/Discord
- Coding test requests requiring file downloads
- GitHub repositories shared during interview process
- npm packages recommended for installation
- References to specific companies: “BlockNovas LLC”, “Angeloper Agency”, “SoftGlideLLC”
Behavioral Analytics
Anomalous User Behavior:
- Developer accessing blockchain explorers at unusual frequency
- npm/GitHub activity followed by blockchain API queries
- Sudden interest in smart contract addresses
- Multiple blockchain explorer queries in short timeframe
- File downloads from professional networking sites
Chrome Enterprise Defensive Policies
1. Block Dangerous Downloads
Policy: DownloadRestrictions
Configuration:
{
"DownloadRestrictions": 1,
"DownloadRestrictions_List": [
"exe",
"msi",
"bat",
"dll",
"cmd",
"scr",
"pif"
]
}
Impact: Prevents execution of malicious payloads even if user clicks fake update prompts
2. Managed Browser Updates
Policy: UpdateDefault
Configuration:
{
"UpdateDefault": 1,
"UpdateSuppressed": {
"Duration": 0,
"StartHour": 0,
"StartMinute": 0
}
}
Impact: Silent automatic updates eliminate social engineering vector of fake update prompts
3. URL Blocklist
Policy: URLBlocklist
Configuration:
{
"URLBlocklist": [
"binplorer.com",
"[known malicious smart contract addresses]",
"[known malicious GitHub repositories]",
"[known malicious npm packages]"
]
}
4. Enhanced Safe Browsing
Policy: SafeBrowsingProtectionLevel
Configuration:
{
"SafeBrowsingProtectionLevel": 2
}
(2 = Enhanced Protection with real-time lookups)
5. Script Execution Controls
Policy: DefaultJavaScriptSetting
Configuration: Restrict JavaScript execution on untrusted sites
npm Package Indicators
Known Malicious Packages
node-nvm-ssh(disguised as chess application “Chessfi”)- Various packages linked to React Native Aria and GlueStack supply chain attack (June 2025)
Detection Pattern
Look for npm packages that:
- Query blockchain APIs
- Include Base64-encoded strings with blockchain addresses
- Make network requests to BNB Smart Chain or Ethereum
- Include XOR decryption routines
- Download additional payloads at runtime
Hunting Queries
Splunk
index=proxy
(bscscan.com OR etherscan.io OR blockchair.com OR blockcypher.com OR ethplorer.io)
| stats count by src_ip, uri
| where count > 10
Microsoft Sentinel (KQL)
DeviceNetworkEvents
| where RemoteUrl contains "bscscan" or RemoteUrl contains "etherscan"
or RemoteUrl contains "blockchair" or RemoteUrl contains "blockcypher"
| summarize QueryCount = count() by DeviceId, RemoteUrl, bin(Timestamp, 1h)
| where QueryCount > 10
Elastic SIEM
event.category:network AND
(destination.domain:(bscscan.com OR etherscan.io OR blockchair.com OR blockcypher.com OR ethplorer.io))
Windows Event Log
Event ID 3 (Network Connection) where:
DestinationPort = 3306 AND
DestinationIp NOT IN [known_database_servers]
Incident Response Checklist
If Compromise Suspected:
Immediate Actions:
- Isolate affected system from network
- Block outbound connections to blockchain APIs
- Disable cryptocurrency wallet browser extensions
- Change all stored passwords
- Revoke all active sessions
Investigation:
- Check browser history for blockchain explorer visits
- Review npm install history
- Examine downloaded files from GitHub/npm
- Check for port 3306 connections in network logs
- Review Telegram/Discord message history
- Identify initial contact (LinkedIn profile, email, etc.)
Cryptocurrency-Specific:
- Transfer cryptocurrency to new wallets with new seed phrases
- Check all wallet transaction history for unauthorized transfers
- Review DeFi protocol approvals and revoke suspicious ones
- Contact exchanges if assets were stolen
- Document theft amounts for law enforcement
Evidence Collection:
- Memory dump of affected system
- Network packet capture
- Browser cache and history
- npm cache contents
- File system timeline
- LinkedIn/Telegram/Discord communication logs
Reporting:
- File report with FBI IC3 (if US-based)
- Report to Google Safe Browsing
- Notify blockchain explorer platforms
- Share IOCs with industry ISACs
- Document for insurance claim (if applicable)
Recommended Security Tools
Blockchain Analysis
- BscScan (https://bscscan.com) - BNB Smart Chain explorer
- Etherscan (https://etherscan.io) - Ethereum explorer
- Chainalysis - Cryptocurrency transaction tracking
- Elliptic - Blockchain forensics
Malware Analysis
- VirusTotal - File and URL scanning
- Hybrid Analysis - Automated malware analysis
- Any.run - Interactive malware sandbox
- Joe Sandbox - Advanced malware analysis
Network Monitoring
- Zeek (formerly Bro) - Network security monitor
- Suricata - IDS/IPS
- Security Onion - Network security monitoring distribution
- Moloch - Packet capture and analysis
Endpoint Protection
- Microsoft Defender for Endpoint
- CrowdStrike Falcon
- SentinelOne
- Carbon Black
Additional Resources
Official Reports
- Google Cloud Blog: https://cloud.google.com/blog/topics/threat-intelligence/dprk-adopts-etherhiding
- MITRE ATT&CK: Dead Drop Resolver (T1102.001)
Blockchain Security
- Trail of Bits: Blockchain security guidance
- OpenZeppelin: Smart contract security
- Consensys Diligence: Security best practices
OSINT Resources
- ThreatFox (abuse.ch): IOC database
- URLhaus: Malicious URL tracking
- MalwareBazaar: Malware sample repository
Contact Information for Threat Intelligence Sharing
Google Threat Intelligence Group:
- Report malicious activity through Google Safe Browsing
Blockchain Explorers:
- BscScan: Contact through platform
- Etherscan: Report malicious contracts
National CERTs:
- US-CERT: us-cert.gov
- NCSC (UK): ncsc.gov.uk
- Other national CERTs as appropriate
Industry ISACs:
- FS-ISAC (Financial Services)
- IT-ISAC (Information Technology)
- Various sector-specific ISACs
Classification: TLP:WHITE (Unlimited distribution) Version: 1.0 Maintainer: [Your Organization] Next Review: November 17, 2025 or upon significant threat developments
This technical reference sheet is provided for defensive purposes only. Organizations are encouraged to use this information to enhance their security posture and detection capabilities.