Executive Summary
On January 3, 2026, the United States executed one of the most sophisticated multi-domain military operations in recent history, resulting in the capture of Venezuelan President Nicolás Maduro. While headlines focus on the dramatic Delta Force raid, the real story lies beneath the surface—in the months of cyber operations, signals intelligence, pattern-of-life analysis, and the unprecedented integration of U.S. Cyber Command and Space Command into kinetic military action.
This analysis examines the cybersecurity, OSINT, and intelligence tradecraft that made Operation Absolute Resolve possible, offering critical insights for security professionals about the modern convergence of cyber warfare and conventional military operations.

Timeline: From Intelligence Gathering to Execution
August 2025: CIA Ground Truth Operations Begin
The CIA covertly deployed a small team into Venezuela to establish what intelligence professionals call “pattern of life” surveillance on Maduro. This ground-truth intelligence gathering focused on:
- Movement patterns and safe house locations
- Daily routines and behavioral habits
- Security protocols and protective details
- Communications patterns and device usage
- Personal details (diet, clothing, even pets)
According to Gen. Dan Caine, Chairman of the Joint Chiefs, the team tracked “how he moved, where he lived, where he traveled, what he ate, what he wore—what were his pets.” This granular intelligence formed the foundation for all subsequent operations.
September-December 2025: Multi-Domain Pressure Campaign
While CIA assets built the intelligence picture, the Trump administration executed a coordinated public and covert pressure campaign demonstrating escalating use of force:
September-December 2025:
- Dozens of strikes on suspected drug vessels in Caribbean and Eastern Pacific (115+ casualties)
- November: Venezuela crude exports peak at 900,000 barrels per day before disruption
- December 10: U.S. Coast Guard seizes sanctioned oil tanker “Skipper” - first-ever seizure of Venezuelan oil cargo
- December 13-15: PDVSA cyberattack - “massive” ransomware operation cripples administrative systems, forces 3-day terminal shutdown
- December 17: Oil loading resumes but exports remain on hold; 15 million barrels stuck on vessels
- December 19: Trump orders naval blockade of all sanctioned tankers - “thousands of troops and nearly a dozen warships” deployed to Caribbean
- Late December: CIA drone strike on Venezuelan coastal dock used by Tren de Aragua gang
- December 23: Trump’s final diplomatic ultimatum call to Maduro
Strategic Effect: This graduated escalation served multiple purposes:
- Degrading Venezuela’s defensive capabilities through persistent disruption
- Testing response times and capabilities of Venezuelan military and cyber defenses
- Signaling U.S. willingness to conduct direct action on Venezuelan soil
- Economic pressure - crude exports fell sharply, creating domestic political pressure
- Intelligence gathering - observing how Venezuela adapted to successive attacks
December 23, 2025: Final Diplomatic Ultimatum
Trump personally called Maduro, offering one last opportunity to leave Venezuela peacefully (with Turkey suggested as destination). Maduro refused, sealing his fate.
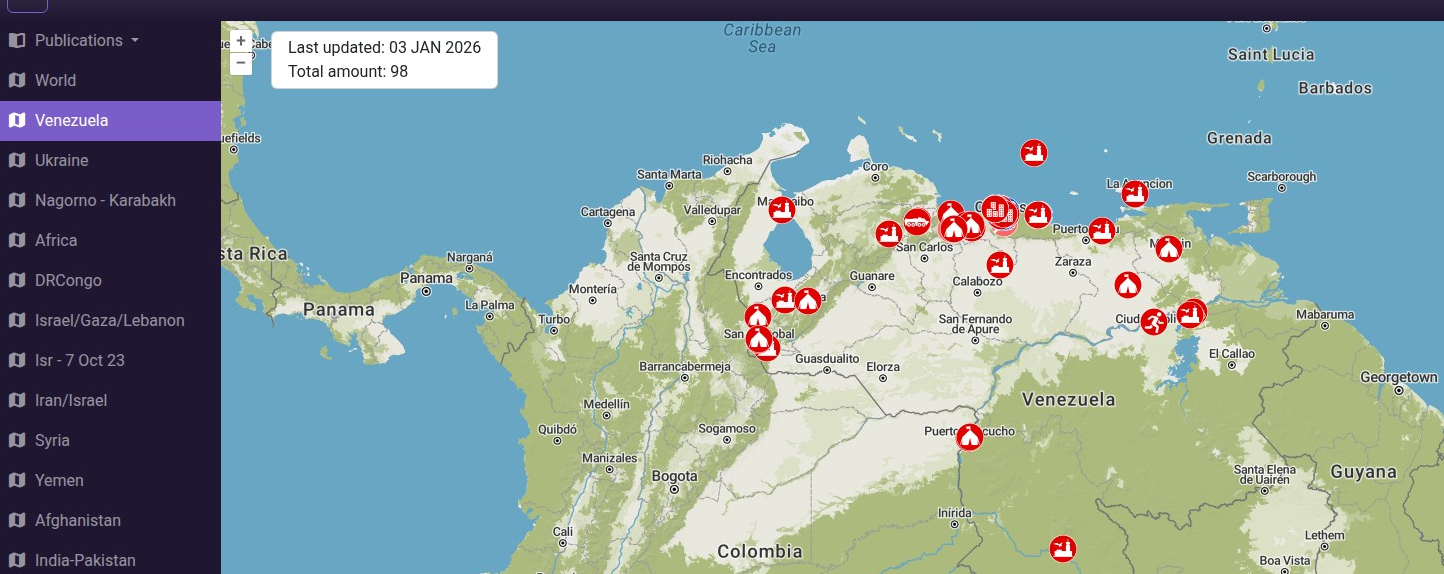
January 2-3, 2026: Operation Absolute Resolve
- 10:46 PM EST, January 2: Trump authorizes the operation
- 150+ aircraft launch from 20 bases across the Western Hemisphere
- 2:01 AM local time (Caracas): Delta Force reaches Maduro’s compound
- Within 30 minutes: Maduro and wife Cilia Flores captured
- 3:20 AM EST: Extraction force clears Venezuelan airspace
The Cyber Operations Component: “Certain Expertise”
Trump’s Cryptic Revelation
During his Mar-a-Lago press conference, President Trump made a telling comment: “It was dark, the lights of Caracas were largely turned off due to a certain expertise that we have.”
This rare public acknowledgment of offensive cyber capabilities provides crucial insights into how U.S. Cyber Command operates in support of kinetic military action.
U.S. Cyber Command’s Role
Gen. Caine confirmed that U.S. Cyber Command, along with Space Command, “began layering different effects” to “create a pathway” for incoming U.S. forces. While officials declined to elaborate on specific tactics, the operational objectives were clear:
- Disrupt power grid infrastructure to provide cover of darkness
- Degrade air defense detection capabilities
- Interfere with Venezuelan military communications
- Support overall operational security and surprise
Technical Attribution and Analysis
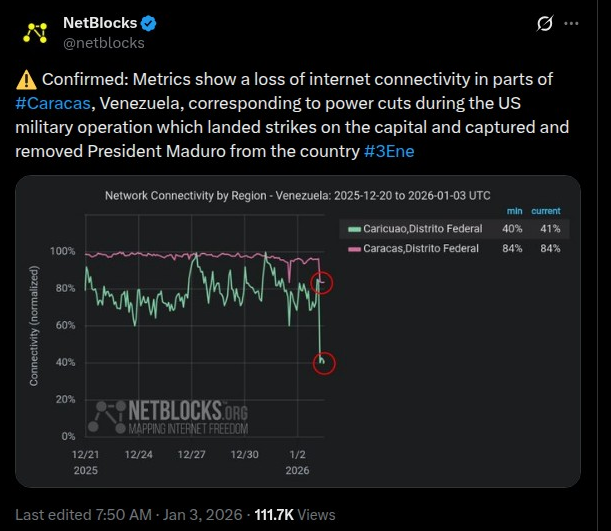
NetBlocks Internet Monitoring Data
NetBlocks, an independent internet observatory, confirmed metrics showing “a loss of internet connectivity in parts of Caracas, Venezuela, corresponding to power cuts during the US military operation.”
Key findings:
- Targeted, not widespread: Alp Toker, NetBlocks founder, noted the outages appeared targeted rather than affecting broader network infrastructure
- Correlation with power disruption: Internet connectivity losses directly correlated with electrical grid failures
- Timing precision: Outages coincided exactly with helicopter insertion phases
⚠️ Confirmed: Metrics show a loss of internet connectivity in parts of #Caracas, Venezuela, corresponding to power cuts during the US military operation which landed strikes on the capital and captured and removed President Maduro from the country #3Ene pic.twitter.com/jk3N3fuazy
— NetBlocks (@netblocks) January 3, 2026
Tor Network Surge
Analysis of Tor Metrics data reveals a significant spike in Venezuelan users accessing the Tor network during and after the operation—a classic indicator of citizens seeking censorship-resistant communications during political crisis and information blackouts.
Comparative Context: Ukraine Cyber-Kinetic Coordination
The Venezuela operation mirrors successful Russian tactics from Ukraine. In November 2023, Mandiant documented how Russian Sandworm hackers tripped circuit breakers at a Ukrainian power substation in coordination with missile strikes—the exact playbook U.S. Cyber Command appears to have adopted.
However, U.S. execution showed greater sophistication:
- Compressed timeline: Power disruption timed to exact minute of aircraft approach
- Surgical targeting: Avoided widespread civilian infrastructure damage
- Multi-domain integration: Cyber effects coordinated with Space Command ISR and kinetic strikes
The OSINT and Intelligence Architecture
Pattern-of-Life Surveillance: CIA Tradecraft at Scale
The CIA’s August-December intelligence gathering operation represents textbook advanced persistent surveillance:
1. Human Intelligence (HUMINT) Asset Development
- Recruited source within Venezuelan government confirmed Maduro’s exact location in real-time during the operation
- $50 million bounty likely facilitated recruitment
- Close-access observation of daily routines, security protocols, facility layouts
2. Signals Intelligence (SIGINT)
- Wiretaps of presidential guard communications
- Device tracking and geolocation
- Communications pattern analysis
3. Imagery Intelligence (IMINT)
- High-resolution satellite imagery for compound mapping
- Stealth drone surveillance fleet providing near-continuous aerial coverage
- Real-time ISR feeds during operation execution
The Full-Scale Replica: Training for Perfection
Delta Force constructed an exact replica of Maduro’s fortified compound, enabling:
- Repeated breach rehearsals until timing was perfect
- Steel door cutting practice with blowtorches
- Multiple contingency scenario testing
- Coordination rehearsals between extraction team and supporting elements
This mirrors the Osama bin Laden operation preparation, where SEAL Team Six trained on a mock-up of the Abbottabad compound.
Multi-INT Fusion: The Intelligence Community Working in Concert
Operation Absolute Resolve showcased unprecedented intelligence fusion:
National Geospatial-Intelligence Agency (NGA): Provided detailed compound mapping and terrain analysis
National Security Agency (NSA): Likely provided SIGINT on Venezuelan military communications and early warning systems
National Reconnaissance Office (NRO): Satellite imagery and overhead surveillance
CIA: Ground truth HUMINT and asset coordination
Defense Intelligence Agency (DIA): Military intelligence support and order of battle analysis
Space Command’s Critical Role: The High Ground
While less publicized than Cyber Command, U.S. Space Command played an equally vital role in “layering effects”:
Satellite Communications (SATCOM)
- Secure, jam-resistant communications for 150+ aircraft coordination
- Real-time data links between Mar-a-Lago situation room and operational commanders
- Encrypted command and control networks
Position, Navigation, and Timing (PNT)
- GPS precision guidance for low-altitude helicopter navigation
- Timing synchronization across 20 launch bases
- Navigation support through mountainous terrain approach
Intelligence, Surveillance, Reconnaissance (ISR)
- Overhead imagery confirming Venezuelan military positions
- Real-time monitoring of air defense systems
- Battle damage assessment during and after strikes
Electronic Warfare (EW) from Space
- Potential jamming of Venezuelan communications satellites
- Signal intelligence collection on military frequencies
- Radar interference supporting air defense suppression
The Air Defense Suppression: Defeating Russian Systems
Venezuela’s air defense architecture included sophisticated Russian and Chinese systems:
- S-300VM long-range surface-to-air missiles
- Buk-M2 medium-range systems
- Pantsir-S1 short-range point defense
- Integrated Chinese radars
How U.S. Forces Achieved Air Superiority
- Standoff Electronic Attack: EA-18G Growlers likely jammed radar systems
- Stealth Penetration: F-22 and F-35 aircraft negated radar detection
- Cyber Disruption: Command and control systems potentially compromised
- Kinetic Strikes: Precision weapons disabled key nodes
- Compressed Timeline: Systems couldn’t generate firing solutions before helicopters departed
This operation sends a clear message to Iran, which fields similar Russian air defense architecture, that layered defenses are increasingly porous against integrated U.S. multi-domain operations.
The PDVSA Cyberattack: December 2025 Context
Attack Timeline and Impact
December 13-15, 2025: PDVSA (Petróleos de Venezuela, S.A.) suffered what it called a “despicable action orchestrated by foreign interests”
According to Politico reporting on December 22, 2025, the attack was described by sources as “massive” and resulted in:
Immediate Impact:
- Temporary blackout at PDVSA - all refineries across country simultaneously lost power
- Telecommunications infrastructure hit - disrupting command and control
- Loading terminal operations suspended for three days (Dec 15-17)
- Ransomware detected - antivirus attempts to remediate affected entire administrative system
- Workers forced to manual record-keeping to resume operations
Operational Disruption:
- Computer virus systematically erased information across network
- Administrative systems targeted (not production control systems)
- PDVSA had to isolate operations of oilfields, refineries, ports from central system
- All loading instructions suspended for export market
- 15 million barrels of Venezuelan oil stuck on vessels in country’s waters
Expert Attribution to U.S. Cyber Command
Multiple former U.S. officials and cyber experts told Politico the attack “bears many of the telltales of a U.S. operation”:
Former federal cyber official (anonymous): “This is what U.S. Cyber Command was built to do. It sounds entirely plausible and is consistent with the mission and capabilities of U.S. Cyber Command.”
PDVSA source with knowledge of attack: “It looks like a preconceived attack… Let’s put it this way, it was not casual—the only groups that are capable of doing that are the U.S.”
Ret. Rear Admiral Mark Montgomery (former director of operations at U.S. Pacific Command): “If this is U.S. offensive cyber operations, then this is the perfect cyber complement to a maximum pressure campaign. Given enough time and opportunity the operation described would be well within U.S. capabilities.”
Key indicators of state-level attribution:
- Simultaneous multi-site impact across geographically distributed facilities
- Precision targeting of administrative vs. production systems
- Integration with ongoing kinetic pressure campaign
- Technical sophistication beyond criminal ransomware operations
Network Architecture Weaknesses Exploited
PDVSA’s vulnerability stemmed from multiple compounding factors:
Sanctions-Induced Technology Isolation:
- Lost access to U.S. security vendor updates and threat intelligence
- No access to incident response vendors for containment/recovery
- Inability to procure modern security tools due to trade restrictions
- Cut off from international cybersecurity community collaboration
Deferred Maintenance Cascade:
- Years of limited IT investment created vulnerability accumulation
- Antivirus software remediation actually spread the infection - indicating outdated security tools
- Legacy systems without modern security features remained in production
- No robust backup/recovery infrastructure - forced manual workarounds
Administrative-Operational Integration Vulnerabilities:
- Export operations required integration between multiple digital layers
- Administrative systems managed export scheduling AND vessel coordination - single point of failure
- José terminal administrative network could paralyze loading without affecting upstream production
- Network segmentation existed but was insufficient against advanced persistent threat
Economic and Strategic Impact
Immediate Commercial Consequences:
- 15 million barrels stuck on vessels in Venezuelan waters (worth ~$1.2 billion at $80/barrel)
- Crude exports fell sharply from 900,000 bpd in November
- Customers demanded price discounts and contract changes for increased shipping risk
- Shadow fleet disruption: 38 of 75 oil tankers under U.S. sanctions, 15 loaded and immobilized
Geopolitical Cascade Effects:
- Russian naphtha exports to Venezuela at risk - needed to dilute extra-heavy crude
- China (primary customer) faced supply disruption - most Venezuela oil bound for Chinese refineries
- Oil prices rose 1%+ globally on threats of deeper, longer-term supply reduction
- Demonstration effect for other sanctioned regimes (Iran, Russia) about infrastructure vulnerability
Ransomware as Operational Cover: Intelligence Collection Under Commercial Crime Guise
The Dual-Purpose Attack Pattern
Reuters reporting revealed PDVSA “detected a ransomware attack” and that “the antivirus software it used to try to fix the problem affected its entire administrative system.” This detail is particularly telling for several reasons:
1. Ransomware Provides Attribution Obfuscation
By deploying ransomware signatures, U.S. Cyber Command could:
- Create ambiguity around state attribution vs. criminal actor
- Provide plausible deniability (“could be any ransomware gang”)
- Delay Venezuelan response as defenders initially treat as criminal incident
- Complicate international condemnation (harder to claim act of war for “criminal” ransomware)
2. Data Exfiltration During Encryption Chaos
While defenders focus on system lockdown and recovery, ransomware deployment provides perfect cover for:
- Exfiltrating operational data: Export schedules, vessel manifests, customer contracts
- Mapping network architecture: Understanding PDVSA’s complete IT environment
- Identifying backup systems: Learning recovery capabilities for future operations
- Intelligence on shadow fleet operations: Routes, captains, shell company structures
3. The “Antivirus Spread” Anomaly
The claim that antivirus software “used to try to fix the problem affected its entire administrative system” suggests several possibilities:
Scenario A - Sophisticated Malware Design: The malware may have been engineered to detect and exploit antivirus remediation attempts, using the cleanup process itself as a distribution mechanism—a technique seen in advanced persistent threat (APT) operations.
Scenario B - Supply Chain Compromise: If PDVSA’s antivirus solution was compromised at the vendor or update server level, remediation attempts could actually deploy additional payloads masquerading as security updates.
Scenario C - Network-Wide Propagation: The malware may have pre-positioned across the network and triggered simultaneously when antivirus scans attempted to quarantine it, creating the appearance that antivirus “spread” the problem.
Historical Precedent: Stuxnet’s Deception Layers
The operation bears similarities to Stuxnet (2009-2010), which the U.S. and Israel used against Iranian nuclear enrichment:
- Appeared benign during initial infection phases
- Hid within legitimate industrial control software
- Collected intelligence on Iranian centrifuge operations before executing
- Multiple failure modes to obscure true purpose and attribution
- Zero-day exploits demonstrated state-level capabilities while maintaining initial deniability
The PDVSA attack may represent an evolution of this playbook for the oil/gas sector.
Attribution Complexity
While PDVSA blamed the U.S. government without providing evidence, multiple indicators point to state-level attribution:
Timing Analysis:
- 3 days after Skipper tanker seizure (Dec 10)
- 8 days before Trump’s blockade order (Dec 19)
- 23 days before Maduro capture operation (Jan 3)
- Pattern suggests coordinated escalation ladder building toward regime change
Technical Sophistication:
- Simultaneous impact across geographically distributed refineries
- Precise targeting of administrative vs. production systems (network segmentation bypass)
- Ransomware deployment as potential cover for data exfiltration
- Scale requiring extensive pre-positioning and network mapping
Operational Pattern Matching: Former senior national security official told Politico: “Trump doesn’t talk about this type of stuff, he thinks it’s nerdy.” This operational security discipline around cyber operations stands in stark contrast to Trump’s public disclosure of the January 3 power grid attack, suggesting:
- December operation was still ongoing or had future applications
- Classification concerns around TTPs used against PDVSA
- Deniability requirements for attacks on civilian infrastructure vs. military targets
The “Nerdy” Blind Spot: Trump’s apparent disinterest in discussing cyber operations may have actually enhanced operational security for the PDVSA attack, preventing the kind of public disclosure that later occurred with the Caracas power grid operation. This creates an interesting dynamic where the president’s lack of cyber fluency inadvertently protected classified capabilities.
Intelligence Lessons and Tradecraft Insights
1. Pattern-of-Life Analysis at Scale
What worked: Five months of continuous surveillance built an unbeatable intelligence picture
Key takeaway: Modern intelligence operations require sustained, multi-INT fusion rather than snapshot assessments
2. Human Intelligence Remains Irreplaceable
Despite billions in technical collection capabilities, a single recruited asset confirmed Maduro’s exact location when it mattered most.
Lesson: Technical intelligence identifies patterns; HUMINT provides ground truth and real-time precision
3. Cyber-Kinetic Integration is the New Normal
The days of siloed military operations are over. Operation Absolute Resolve demonstrates that:
- Cyber effects enable kinetic operations (power disruption covering aircraft approach)
- Kinetic strikes protect cyber operators (air defense suppression)
- Space-based systems integrate both (communications, navigation, ISR)
4. OPSEC Discipline Under Extreme Political Pressure
Despite months of planning and hundreds of personnel involved, the operation maintained complete tactical surprise. Congressional notification occurred only after forces were airborne, preventing leaks.
Critical factor: Trump’s willingness to bypass traditional congressional briefings to maintain operational security
Defensive Implications for Critical Infrastructure
What Venezuela’s Experience Teaches CISOs
1. Air-Gapping is Insufficient
PDVSA attempted to protect production systems through network segmentation, but administrative systems controlling exports provided adequate attack surface.
Lesson: Modern critical infrastructure requires integration that creates unavoidable cyber vulnerabilities—defense must assume breach, not prevent access.
2. Sanctions Create Compound Cyber Risk
Venezuela’s isolation from Western technology vendors created:
- Inability to access security patches
- No access to incident response vendors
- Degraded threat intelligence
- Legacy system persistence
Lesson: Geopolitical isolation dramatically amplifies cyber risk—organizations operating in sanctioned regimes face exponentially greater threats.
3. Power Grid Cybersecurity Remains Critical
The Caracas power disruption, whether purely cyber or cyber-assisted kinetic, demonstrates that electrical grid control systems remain viable military targets.
Recommendations:
- Implement zero-trust architectures for SCADA systems
- Deploy out-of-band monitoring for early intrusion detection
- Maintain manual override capabilities for critical switching
- Practice grid black-start procedures regularly
- Harden communications infrastructure against jamming
The Broader Geopolitical Cyber Landscape
Messages Sent to Adversaries
To Iran:
U.S. forces can penetrate Russian air defense systems similar to those protecting Iranian nuclear facilities. The Venezuela operation serves as a demonstration of capability.
To China:
Multi-domain coordination at this scale suggests U.S. readiness for Taiwan contingencies, despite the vast operational differences.
To Russia:
The U.S. can execute Russian-style cyber-kinetic coordination at a higher level of precision and integration. For comparison with recent Russian hybrid warfare operations, see: Denmark Accuses Russia of Cyber-Attacks Targeting Critical Infrastructure and Elections
The “Trump Corollary” to the Monroe Doctrine
The operation represents a reestablishment of U.S. hemispheric dominance through demonstrated capability rather than diplomatic posturing.
As outlined in the 2025 National Security Strategy: The Western Hemisphere is a U.S. security priority where direct military action remains an option.
Operational Security and Information Warfare
The Information Battlespace
Trump’s Unprecedented Transparency
Unlike typical covert operations, Trump publicly released:
- Photos of Maduro in custody (blindfolded, handcuffed, in gray sweatpants)
- Operational videos posted to Truth Social
- Real-time social media monitoring feeds from the Mar-a-Lago situation room
- Detailed operational briefing within hours of mission completion
Strategic purpose:
- Deter future adversaries through demonstration of capability
- Shape international narrative before opponents can establish counter-narratives
- Satisfy domestic political demands for transparency
- Showcase U.S. military superiority to global audience
Congressional Notification Controversy
Democratic lawmakers accused Secretary of State Marco Rubio and Defense Secretary Pete Hegseth of lying during a December Senate briefing where they claimed regime change wasn’t the goal.
OPSEC vs. Oversight: The tension between constitutional oversight and operational security remains unresolved.
Technical Deep Dive: Probable Cyber TTPs
Hypothesis: How U.S. Cyber Command Disrupted Caracas Power
Based on available evidence and comparative operations (Ukraine, Iran), likely attack vectors included:
1. SCADA System Compromise
Potential TTPs:
- Initial access: Spear-phishing of electrical utility employees
- Persistence: Implants in SCADA management networks
- Lateral movement: Exploitation of flat network architectures common in aging infrastructure
- Impact: Remote manipulation of circuit breakers and relay systems
2. Physical-Cyber Hybrid Attack
Alternative scenario:
- Pre-positioned assets: CIA team with physical access to critical substations
- Insider access: Recruited utility employees providing credentials
- Manual switching: Physical disconnection coordinated with cyber signals
- Kinetic strikes: Precision munitions on key transmission nodes
3. Satellite Communication Jamming
Space Command contribution:
- GPS interference: Disrupting precision timing for grid synchronization
- SATCOM denial: Blocking remote monitoring and control systems
- EW coordination: Creating electromagnetic “noise” preventing grid management communications
Most Likely Scenario: Multi-Vector Integration
The phrase “layering different effects” suggests all three approaches were employed simultaneously:
- Cyber Command compromised control systems
- CIA assets provided physical access where needed
- Space Command ensured communications blackout
- Kinetic strikes destroyed backup systems
Lessons for Cybersecurity Professionals
1. Nation-State Offensive Capabilities Continue to Evolve
The Venezuela operation demonstrates several cutting-edge capabilities:
- Cyber-kinetic synchronization at minute-level precision
- Multi-domain command and control across cyber, space, air, and ground
- Real-time intelligence fusion enabling adaptive operations
For defenders: Assume adversaries (especially Five Eyes nations) possess capabilities far beyond publicly acknowledged techniques.
2. Critical Infrastructure Protection Requires Whole-of-Nation Approach
PDVSA’s failure stemmed from isolation, not just technical shortcomings. Effective critical infrastructure defense requires:
- International cooperation on threat intelligence
- Access to cutting-edge defensive tools
- Skilled workforce with current training
- Regulatory framework enabling security investments
3. Offensive Cyber Operations Are Becoming Routine Military Tools
Just as electronic warfare became standard in 20th-century conflicts, 21st-century military operations assume cyber domain integration.
Implication: Organizations must plan for adversary use of cyber capabilities in any conflict scenario affecting their region or sector.
4. OSINT Provides Unprecedented Transparency
Despite operational secrecy, public sources (NetBlocks, social media, commercial satellite imagery) provided near-real-time awareness of the operation.
For security professionals:
- OSINT is both threat and opportunity—adversaries can track your infrastructure, but you can monitor theirs
- Assume your operations are visible to sophisticated OSINT practitioners
- Invest in OSINT capabilities for threat intelligence and early warning
5. The December “Softening” Campaign Enabled January Success
The PDVSA cyberattack three weeks before the Maduro capture was not an isolated event but rather a critical component of operational preparation:
Intelligence Collection:
- Ransomware deployment provided cover for mapping PDVSA’s entire IT architecture
- Understanding administrative vs. operational system separation informed January power grid targeting
- Shadow fleet data exfiltration revealed shipping patterns and evasion tactics
Defensive Capability Assessment:
- Observed how quickly Venezuela could detect and respond to cyber intrusion
- Tested resilience of backup systems and manual workarounds
- Assessed international response timelines and diplomatic consequences
Psychological Operations:
- Created climate of uncertainty among Venezuelan leadership
- Demonstrated U.S. capability to strike anywhere, anytime
- Primed international community for escalation without triggering immediate intervention
Operational Precedent:
- Established that cyber attacks on civilian infrastructure wouldn’t trigger Article 5-level international response
- Normalized graduated escalation pattern that continued through January
- Provided legal and political cover for subsequent power grid operation (“we’ve been doing this for weeks”)
This multi-week campaign demonstrates that modern military operations begin in cyberspace long before kinetic forces deploy.
The Future: Cyber Operations in Multi-Domain Warfare
Emerging Trends from Operation Absolute Resolve
1. Cyber as Enabler, Not Standalone Capability
The Venezuela operation shows cyber effects are most powerful when integrated with kinetic operations, not as isolated attacks.
Trend: Expect future conflicts to feature cyber-kinetic combinations where:
- Cyber creates windows of opportunity
- Kinetic forces exploit those windows
- Space-based systems coordinate both
2. Precision Timing Becomes Critical
The operation’s success depended on minute-level coordination across:
- 150+ aircraft
- 20 launch bases
- Multiple time zones
- Cyber effects timing
- Intelligence asset positioning
Implication: Future cyber operations will require increasingly precise timing coordination with conventional forces.
3. Space Command Centrality to Multi-Domain Operations
Space-based capabilities provided the “connective tissue” enabling the entire operation:
- Communications
- Navigation
- Intelligence
- Electronic warfare
Forecast: Space domain superiority will become prerequisite for advanced cyber-kinetic operations.
Recommendations for Security Leaders
For CISOs Protecting Critical Infrastructure
- Assume state-level adversaries can coordinate cyber-kinetic attacks on your infrastructure
- Implement defense-in-depth assuming air-gapped protections will be breached
- Develop manual override procedures for all critical systems
- Establish out-of-band communications that don’t rely on commercial internet
- Participate in sector-wide information sharing to improve collective defense
- For broader context on critical infrastructure threats, see our comprehensive analysis: Critical Infrastructure Under Siege: 2024-2025 Cybersecurity Landscape
For Intelligence Professionals
- Invest in HUMINT recruitment alongside technical collection
- Build pattern-of-life analysis capabilities for long-term target development
- Develop multi-INT fusion centers that break down analytical silos
- Prepare for cyber-kinetic integrated operations in your planning
For Policymakers
- Establish clear legal frameworks for cyber operations in support of kinetic action
- Balance operational security with congressional oversight requirements
- Develop international norms for cyber-kinetic operations against civilian infrastructure
- Invest in cyber workforce development to maintain U.S. advantages
Conclusion: The New Era of Integrated Warfare
Operation Absolute Resolve marks a watershed moment in modern warfare—the first time the U.S. has publicly acknowledged offensive cyber operations in direct support of a regime change mission. The operation’s success demonstrates several critical realities:
For offensive operators: Cyber-kinetic integration provides overwhelming advantages when properly coordinated across domains.
For defenders: Traditional defensive paradigms (air-gapping, network segmentation, perimeter security) are necessary but insufficient against state-level multi-domain attacks. For comprehensive analysis of the 2025 threat landscape, see: Briefing: 2025 Cybersecurity Threat Landscape and Incident Analysis
For the security community: We must fundamentally rethink critical infrastructure protection in an era where adversaries can coordinate cyber attacks with kinetic military operations, space-based effects, and human intelligence assets.
The capture of Nicolás Maduro will be studied for decades as a template for modern multi-domain operations. For cybersecurity professionals, the lesson is clear: the integration of cyber, space, intelligence, and kinetic capabilities represents the future of both offensive operations and the threats we must defend against.
As we continue to analyze this operation, one thing is certain—the lines between cyberspace operations, traditional military action, and intelligence gathering have permanently blurred. Security professionals who understand this integration will be positioned to defend against tomorrow’s threats; those who don’t will be defending yesterday’s battlespace.
References and Further Reading
Primary Sources
- Gen. Dan Caine press conference, Mar-a-Lago, January 3, 2026
- President Trump Truth Social posts and press statements
- NetBlocks internet monitoring data and analysis
- U.S. Department of Justice indictment (Southern District of New York)
December 2025 PDVSA Cyberattack
- POLITICO: “A who-done-it in Venezuelan cyberspace” by Maggie Miller, Daniella Cheslow, and Giselle Ruhiyyih Ewing (December 22, 2025)
- Reuters: “Oil tanker loading resumes in Venezuela, but most exports on hold” by Marianna Parraga (December 17, 2025)
- Multiple unnamed former U.S. cyber officials and national security experts
Analysis and Reporting
- CNN: “From order to extraction: Inside the US capture of Nicolás Maduro”
- The New York Times: CIA operations and cyberattack reporting
- NBC News: “A CIA team, steel doors and a fateful phone call”
- POLITICO: “Trump suggests US used cyberattacks to turn off lights in Venezuela”
- DefenseScoop: “US deploys 150-plus military aircraft, drones and other tech”
- Breaking Defense: “150 aircraft, cyber effects and ‘overwhelming force‘“
Technical Analysis
- NetBlocks internet disruption metrics and methodology
- Tor Metrics Venezuelan user data
- Dark Reading: “US Action in Venezuela Provokes Cyberattack Speculation”
- Bank Info Security: Analysis of power grid cyberattack attribution
- TankerTrackers.com: Shadow fleet monitoring data
Expert Commentary
- Ret. Rear Admiral Mark Montgomery (Foundation for Defense of Democracies)
- Multiple anonymous former U.S. Cyber Command officials
- Former senior national security officials (offensive cyber operations)
Background and Context
- December 2025 PDVSA cyberattack reporting (Reuters, Bloomberg, Politico)
- Mandiant analysis of Russian cyber-kinetic operations in Ukraine
- Atlantic Council: “Experts react: The US just captured Maduro”
- Stuxnet historical analysis and comparisons
Disclaimer: This analysis is based on publicly available information and open-source intelligence. Classified details of U.S. cyber operations remain unknown. This article is intended for educational and analytical purposes to inform cybersecurity professionals about emerging threats and operational trends.
Related Reading from the CISO Marketplace Network
Critical Infrastructure and Hybrid Warfare
- Shadow Fleet Strikes Again: Finland Seizes Turkish-Managed Vessel After Baltic Cable Damage - Deep dive into Russia’s shadow fleet operations targeting undersea telecommunications infrastructure in the Baltic Sea, demonstrating hybrid warfare tactics similar to those analyzed in the Venezuela operation
- Denmark Accuses Russia of Cyber-Attacks Targeting Critical Infrastructure and Elections - Analysis of Russian hybrid warfare campaign including water infrastructure SCADA manipulation and DDoS attacks during elections, providing comparative context for state-level cyber operations
- Critical Infrastructure Under Siege: 2024-2025 Cybersecurity Landscape - Comprehensive overview of attacks on dams, power grids, and essential services, contextualizing the Venezuela power grid attack within broader critical infrastructure threat trends
2025 Threat Landscape
- Briefing: 2025 Cybersecurity Threat Landscape and Incident Analysis - Executive briefing on 2025 attack trends showing 50% of ransomware targeting critical infrastructure, relevant to understanding PDVSA attack patterns
- France Opens Intelligence Investigation After Pro-Russian Hackers Claim Responsibility for Christmas Postal Service Cyberattack - Analysis of NoName057(16) operations against French critical services, demonstrating state-sponsored DDoS tactics for geopolitical objectives
Government and State-Sponsored Operations
- Russia-Linked Cyberattack Exposes Critical Vulnerabilities in Federal Court Systems - Russian FSB breach of U.S. federal judiciary systems, illustrating long-term intelligence collection operations against government infrastructure
- French Interior Ministry Email Servers Breached in Latest Government Cyberattack - Government email infrastructure targeting showing persistent threat environment facing national security agencies